Single Sign-On (SSO) lets organization Owners and Admins enforce centralized authentication for all GitKraken users on verified email domains. SSO is supported only for GitKraken cloud organizations; On-Premise plans are not supported.
Once your organization has set up SSO with an Identity Provider (IdP), the Owner or an Admin can link the GitKraken organization to that IdP. After linking, users associated with the IdP can log in to GitKraken apps and services.
SSO is available with a GitKraken Advanced, Business, or Enterprise subscription. It is also included in the 30-day multi-user trial.
Quick Start
GitKraken SSO uses SAML 2.0.
To configure SSO for your organization:
- Sign in at gitkraken.dev as an Owner or Admin.
- Navigate to Settings > Single sign-on and click Set up SSO.
- Enter a connection name, your base domain (e.g.,
yourcompany.com), and credentials from your IdP: Metadata URL, raw Metadata, or Certificate. - Click Create Connection.
- Add the provided DNS TXT record at your domain registrar, then return to GitKraken.dev and click Verify Ownership.
- Enable the SSO toggle. Optionally enable Just-in-time (JIT) provisioning to auto-add verified users on first login.
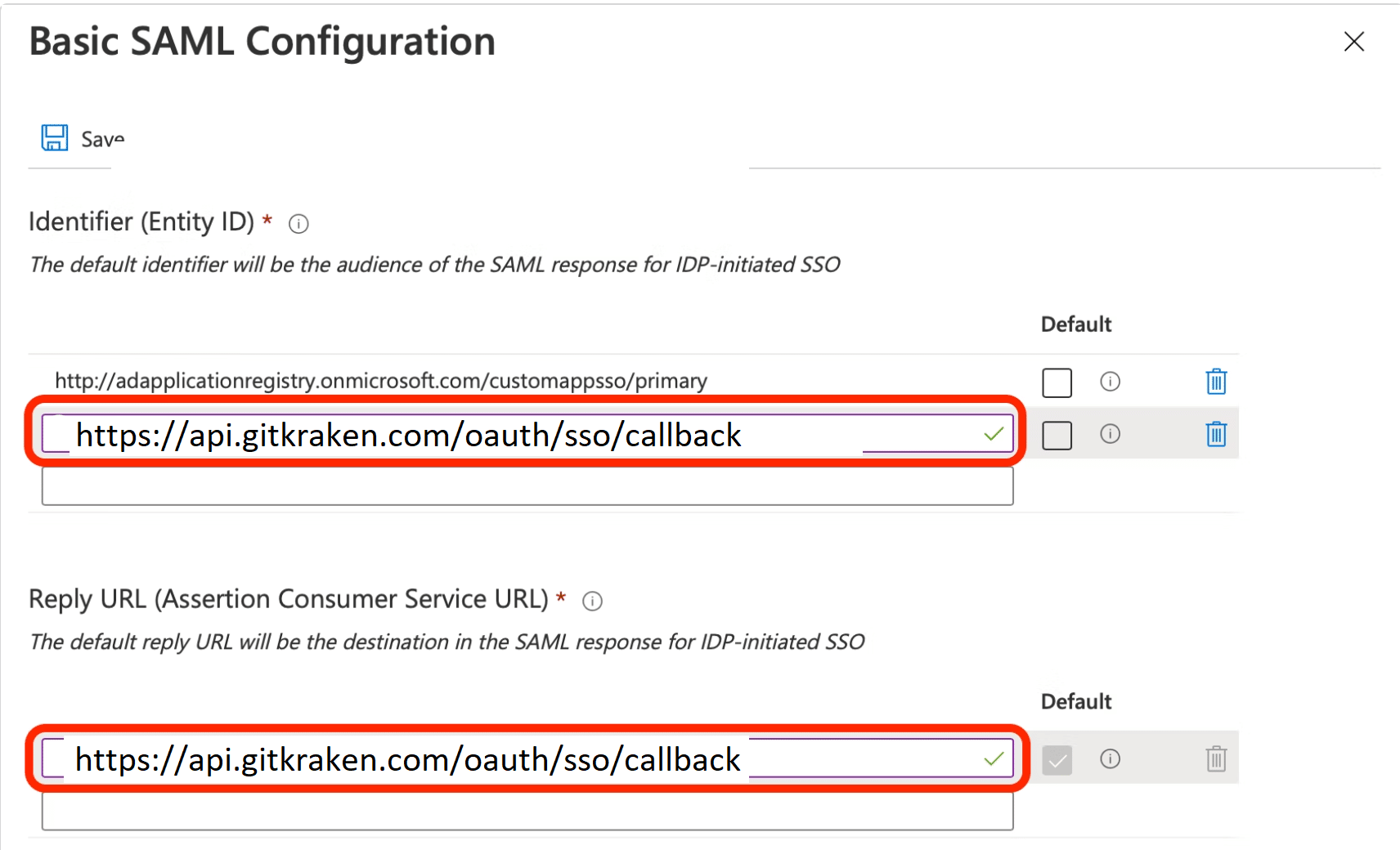
The SSO callback URL for all IdPs is https://api.gitkraken.com/oauth/sso/callback.
What is single sign-on (SSO)?
Single sign-on (SSO) is an authentication method that lets users sign in once and gain access to multiple, independent software systems without needing to re-enter their credentials.
Here are some important terms related to SSO:
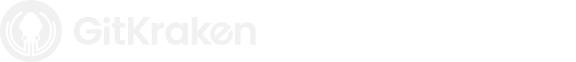
Directory Server: A directory server stores information about organizational “objects” such as printers, computers, shared folders, users, or groups. These objects may be organized hierarchically.
Examples:
Identity Provider (IdP): An IdP manages identity information and provides authentication services. It stores users, groups, and apps that rely on it to authenticate logins.
Examples:
Identity providers authenticate users on behalf of other apps, using a protocol called OAuth. This ensures the third-party apps can verify a user without needing access to their password.
Third-party applications: These are the services that use an IdP to authenticate users. Users are redirected to the IdP to log in, then returned to the application once verified.
Examples:
How SSO works in GitKraken
GitKraken is a third-party application in this context. The Owner or an Admin of a GitKraken organization can set up SSO.
Which identity providers does GitKraken support?
GitKraken supports SAML 2.0 for SSO. Any identity provider (IdP) that supports SAML 2.0 is compatible.
Which plans include SSO?
SSO requires a GitKraken Advanced, Business, or Enterprise subscription, or a 30-day multi-user trial. To support multiple domains, GitKraken Enterprise or the multi-user trial is required.
How SSO enforcement works
-
SSO is enforced at the domain level:
- Users whose account emails match a verified SSO domain must log in via SSO.
- Owners and Admins can log in using any method.
-
SSO is also enforced at the organization level:
- All users matching a verified domain must be part of the GitKraken organization.
- Users with unmatched domains must be removed before SSO can be enabled.
-
Additional rules:
- Users cannot create other organizations or subscriptions.
- Users cannot leave the organization or change their email/password.
- Existing accounts with other organizations/subscriptions can keep them, but can’t access them until they are part of the organization and sign in with SSO.
How just-in-time provisioning (JIT) works
JIT can be enabled at GitKraken.dev > Settings > SSO. When JIT is active and a user logs in successfully via SSO, they will automatically join the organization and consume a license.
Note: JIT only works if there are available licenses. If none are available, users will not be added.
What the SSO login experience looks like
- On the login screen, select SSO to sign in.
- If a user tries to log in using a method other than SSO and matches a managed domain, they’ll see a message requiring SSO.
- If a user logs in with SSO but is not part of the organization, they’ll be prompted to contact an admin.
- Owners and Admins may sign in using any supported method.
GitKraken SSO does not support signing in through the Identity Provider’s dashboard.
Set up SSO
- Log in to GitKraken.dev as an Owner or Admin.
- Navigate to Settings > Single sign-on in the left sidebar.
- Click Set up SSO.
- If existing connections appear, you may delete them to start from a blank state.
- Complete the connection form:
- Connection name: Name shown to users in GitKraken.
- Domain: Use the base domain (e.g., gitkraken.com).
- Identity URL: Provided by GitKraken, paste this into your IdP.
- Credentials: Choose Metadata URL, raw Metadata, or Certificate. Paste in values from your IdP.
- Click Create Connection when done.
- Verify domain ownership:
- Copy the TXT record provided.
- Log in to your DNS provider and add the record.
- Return to GitKraken and click Verify Ownership.
- Note: DNS changes may take minutes or hours to propagate.
- (Optional) Add additional domains:
- If users span multiple domains, click Add Connection and repeat steps 4 and 5.
- Enable SSO:
- Ensure connections in the table are enabled (the presence of Disable means it is enabled).
- Turn on the Enable SSO switch at the top.
- You may be prompted to remove users with unmatched domains or to add external GitKraken users to your organization.
- You may cancel and add more domains if needed.
- (Optional) Enable JIT to allow new users to auto-join when signing in with SSO (requires available licenses).
SSO is now enabled and enforced across GitKraken for your domains. Be sure to test your setup. If you run into issues, contact GitKraken support.
Example Identity Provider (IdP) setup instructions
Note: These are example instructions to help you with Identity Provider setup. In most cases all you will need from us is the callback URL: https://api.gitkraken.com/oauth/sso/callback. If you need assistance please contact your IdP administrator or consult the IdP documentation for help.
G Suite
How to Create a SAML Application in G Suite:
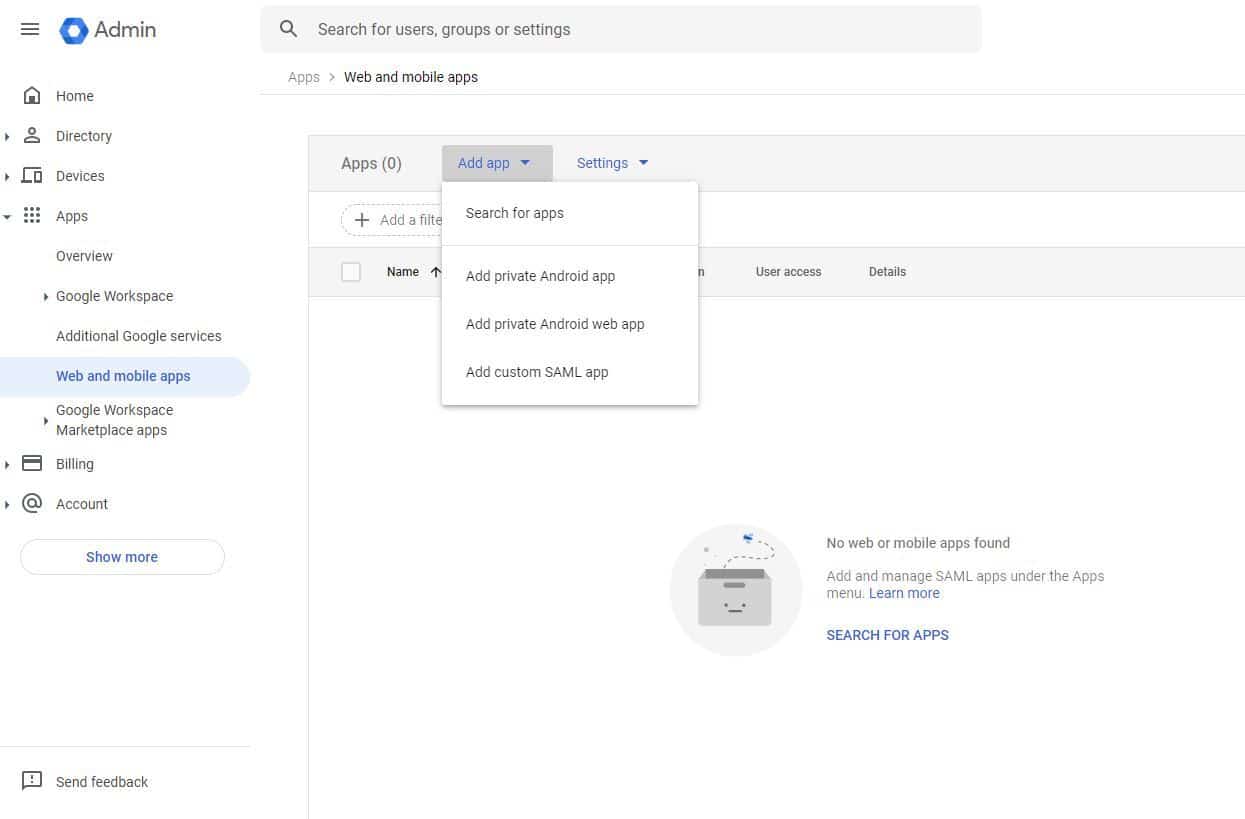
- Go to https://admin.google.com/
- Click on Apps and then Web and mobile apps.
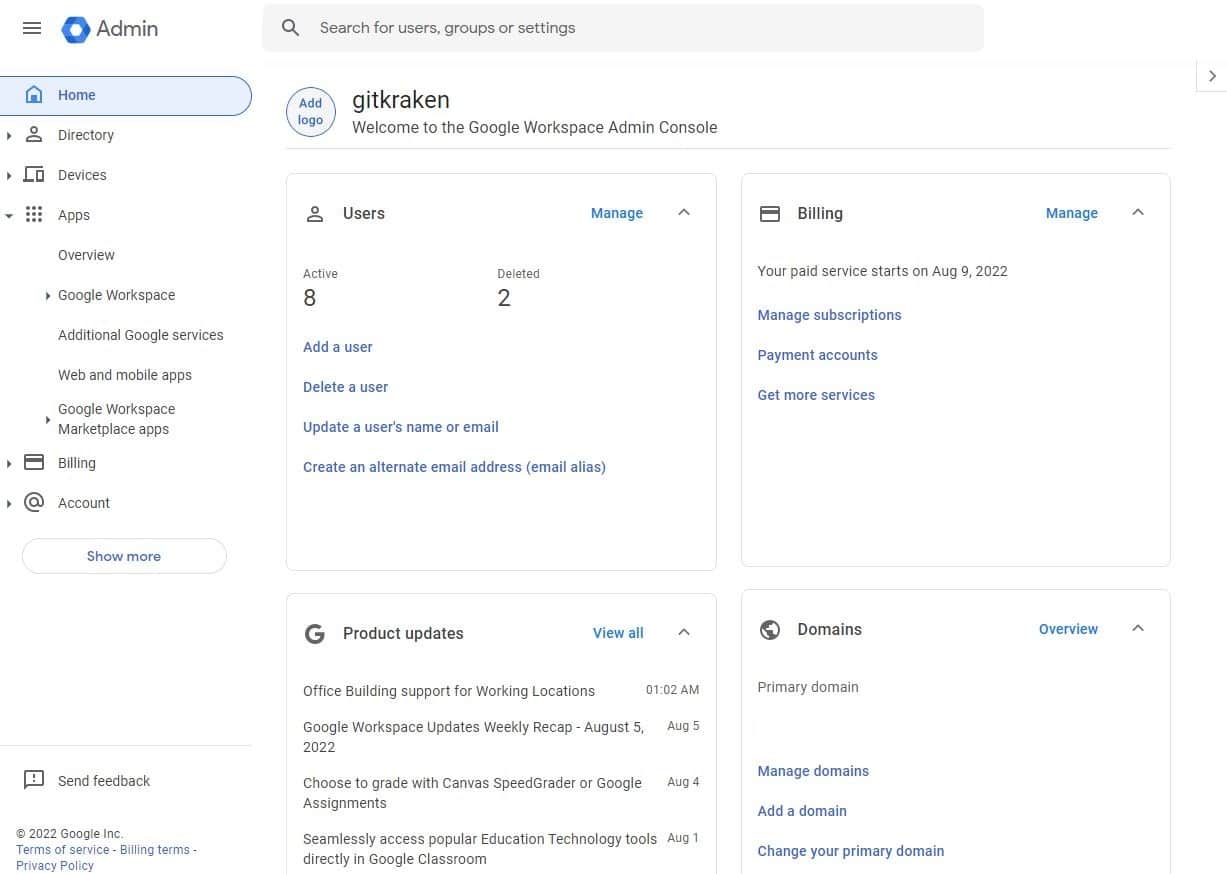
Navigate to Web and mobile apps - Click on Add app.
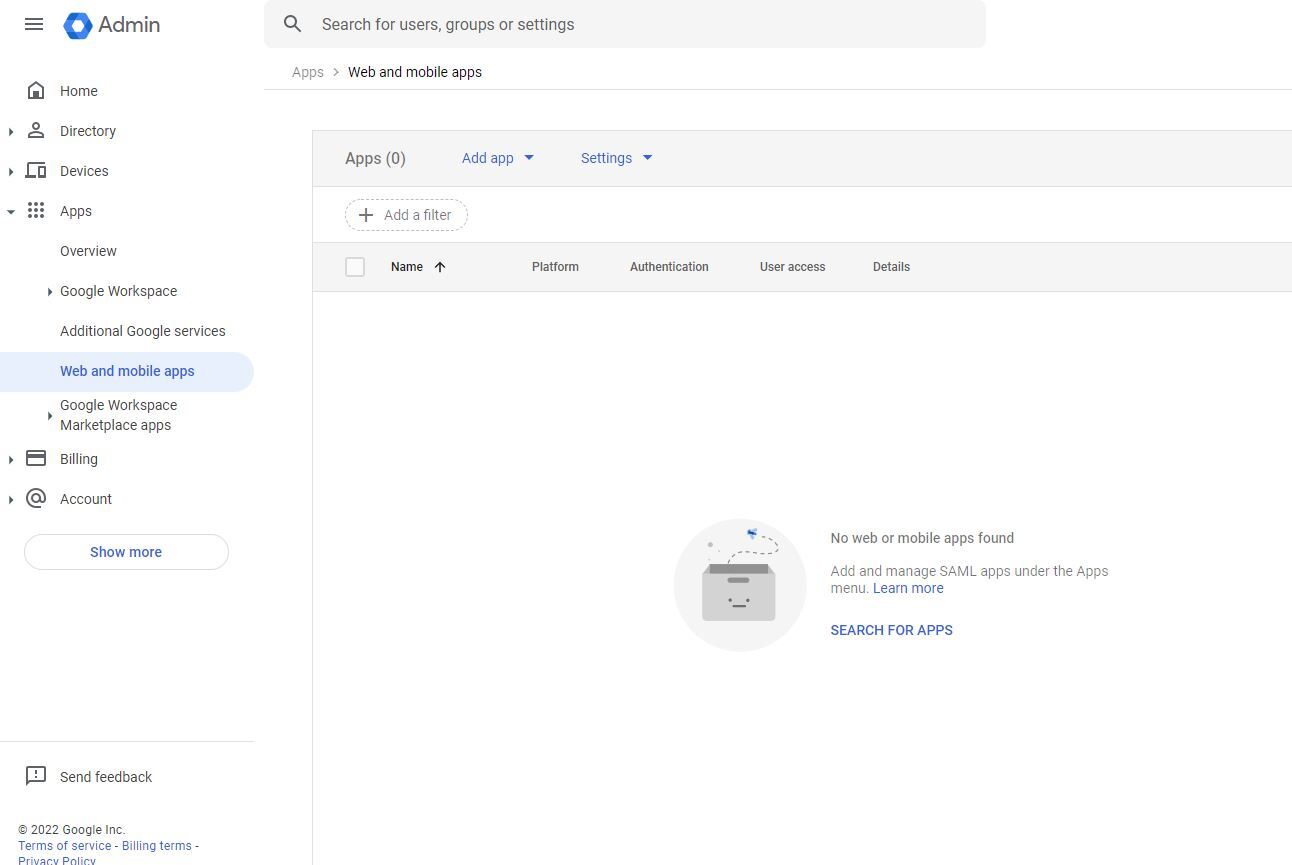
Add a new application - Click Add custom SAML app.
Choose to add a custom SAML app - Type in your app name (e.g., GitKraken SSO).
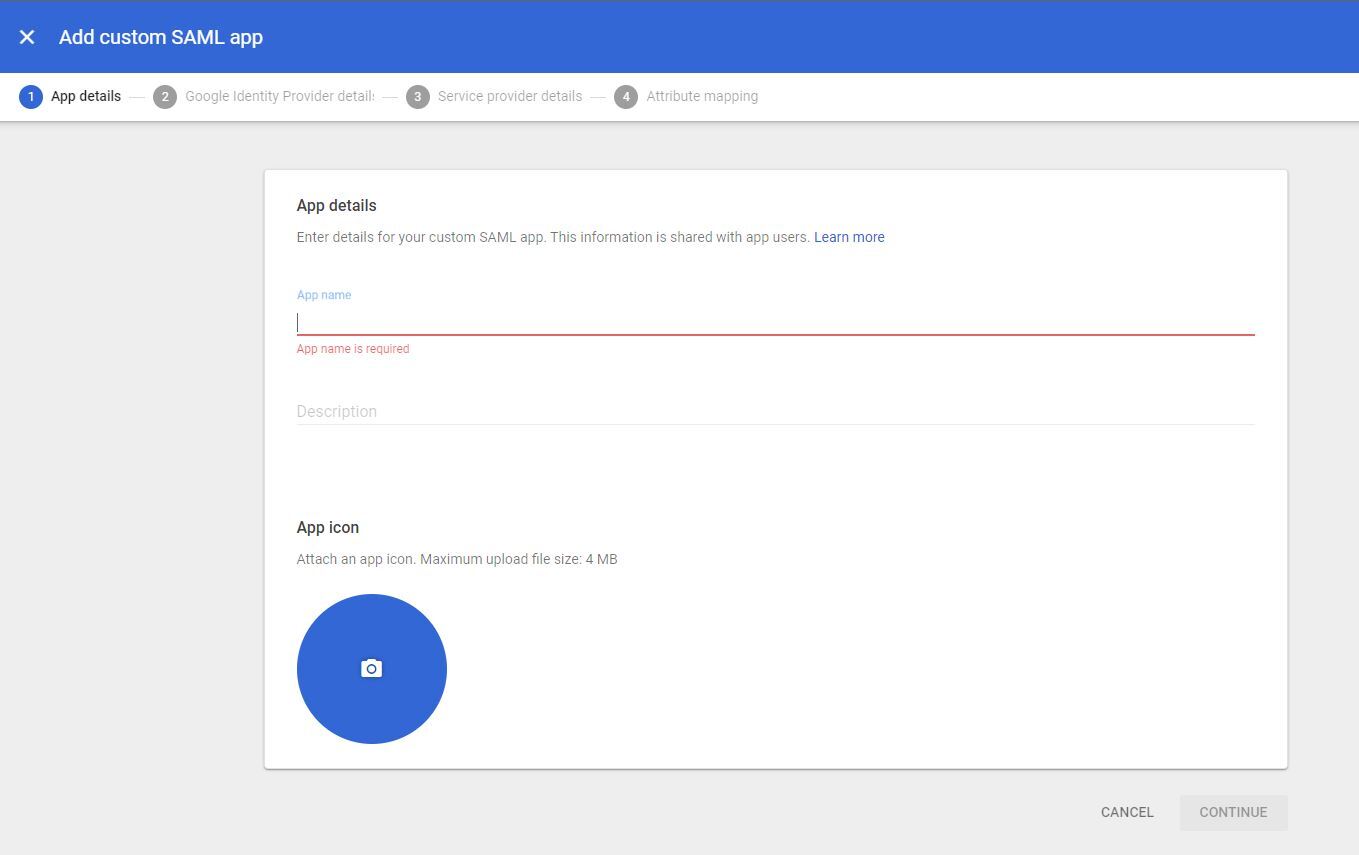
Name your SAML app - Copy your SSO URL and Certificate.
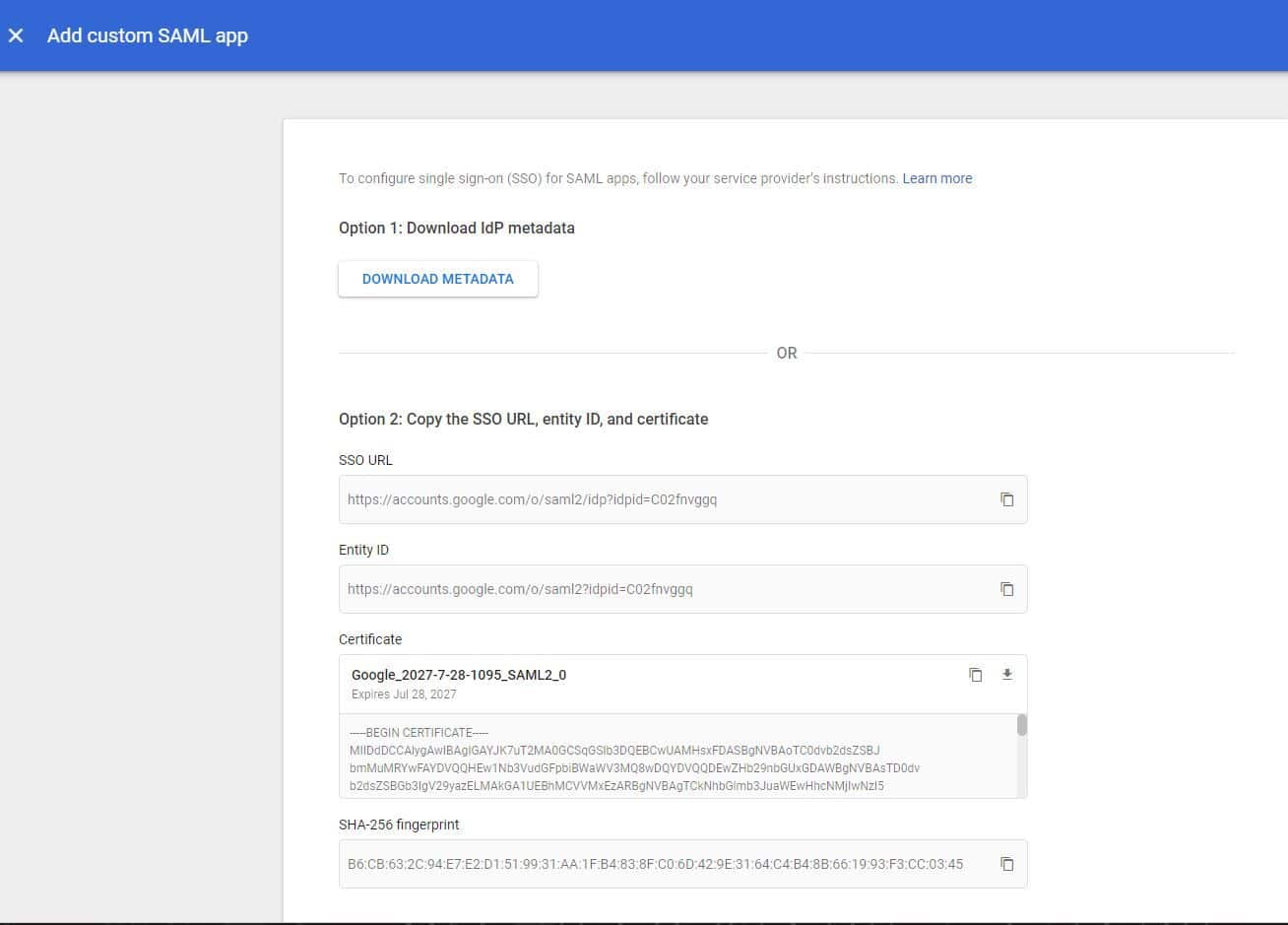
Retrieve SSO URL and certificate - Enter the callback URL
https://api.gitkraken.com/oauth/sso/callbackfor both ACS URL and Entity ID.
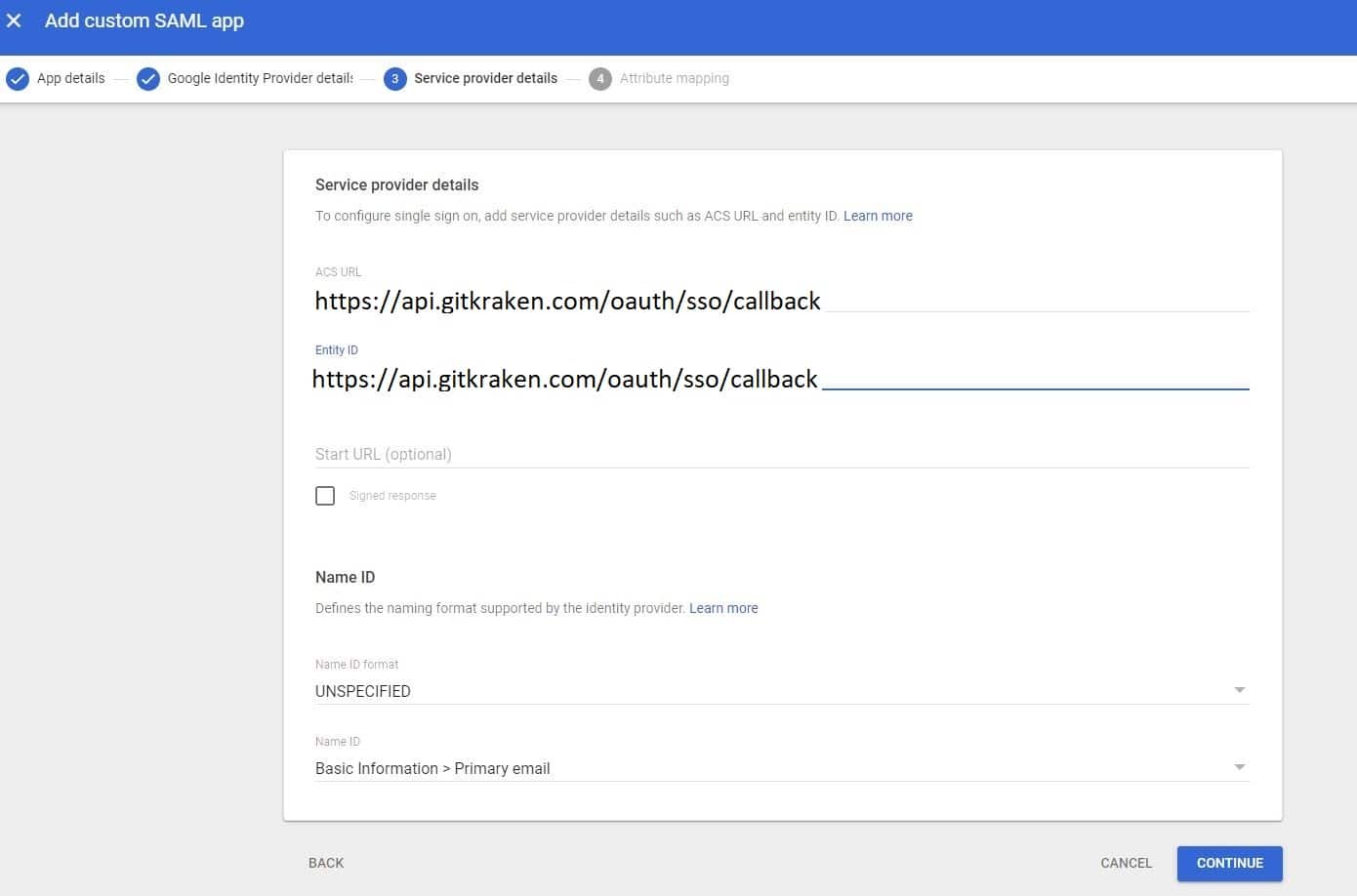
Input ACS URL and Entity ID - Add desired attributes and click Finish.
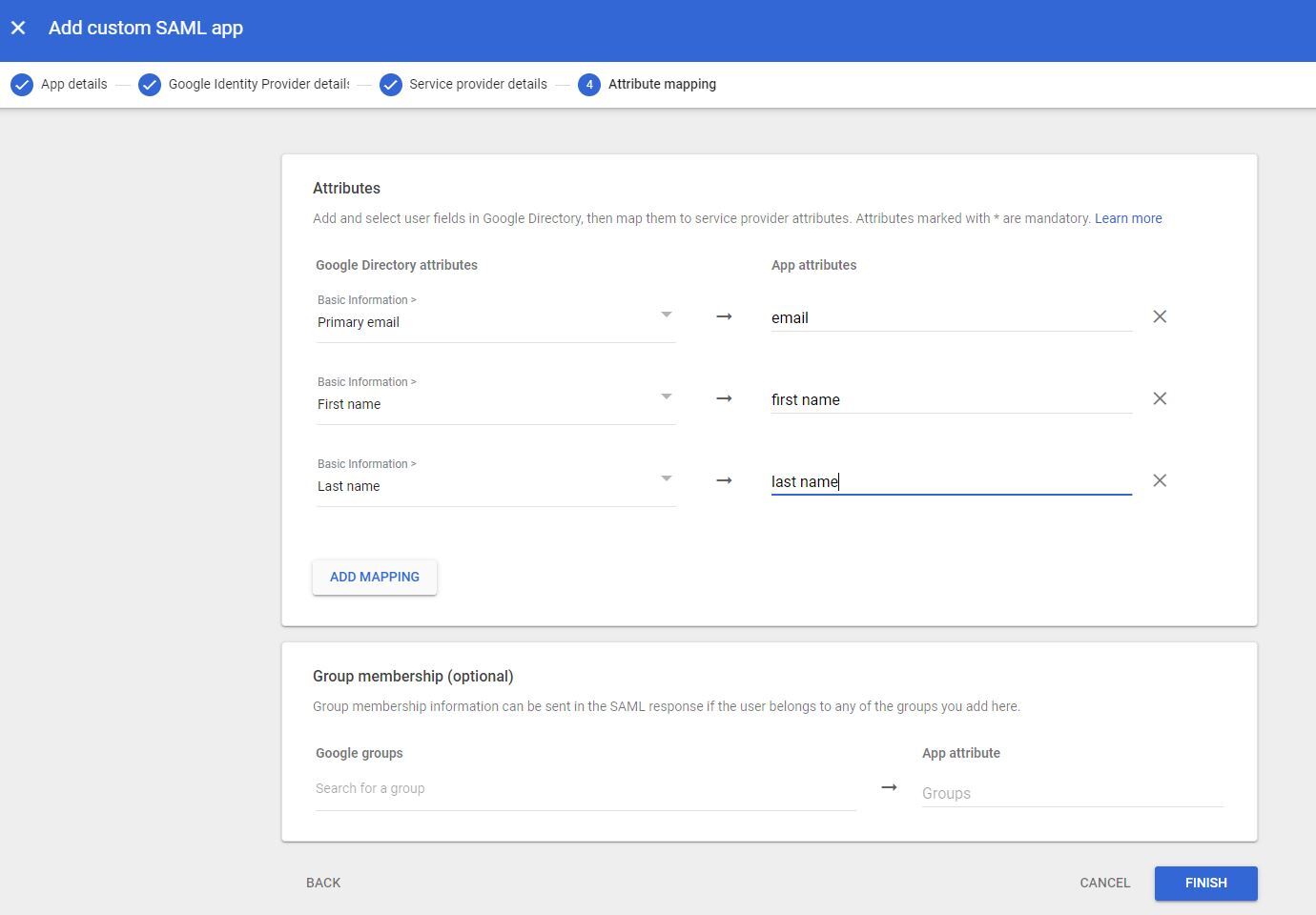
Configure attributes - Click TEST SAML LOGIN.
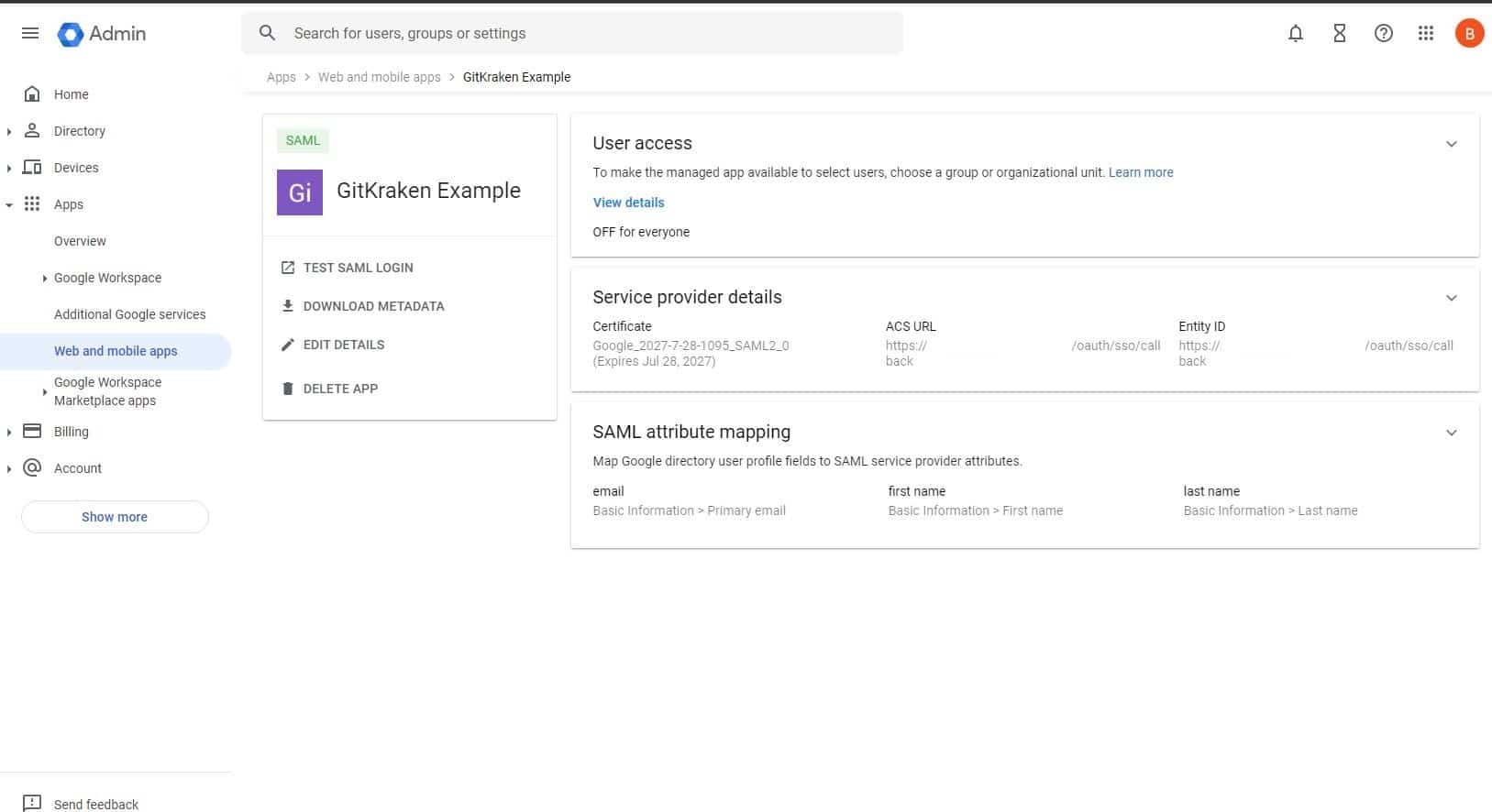
Test your SAML login - Click ALLOW ACCESS.
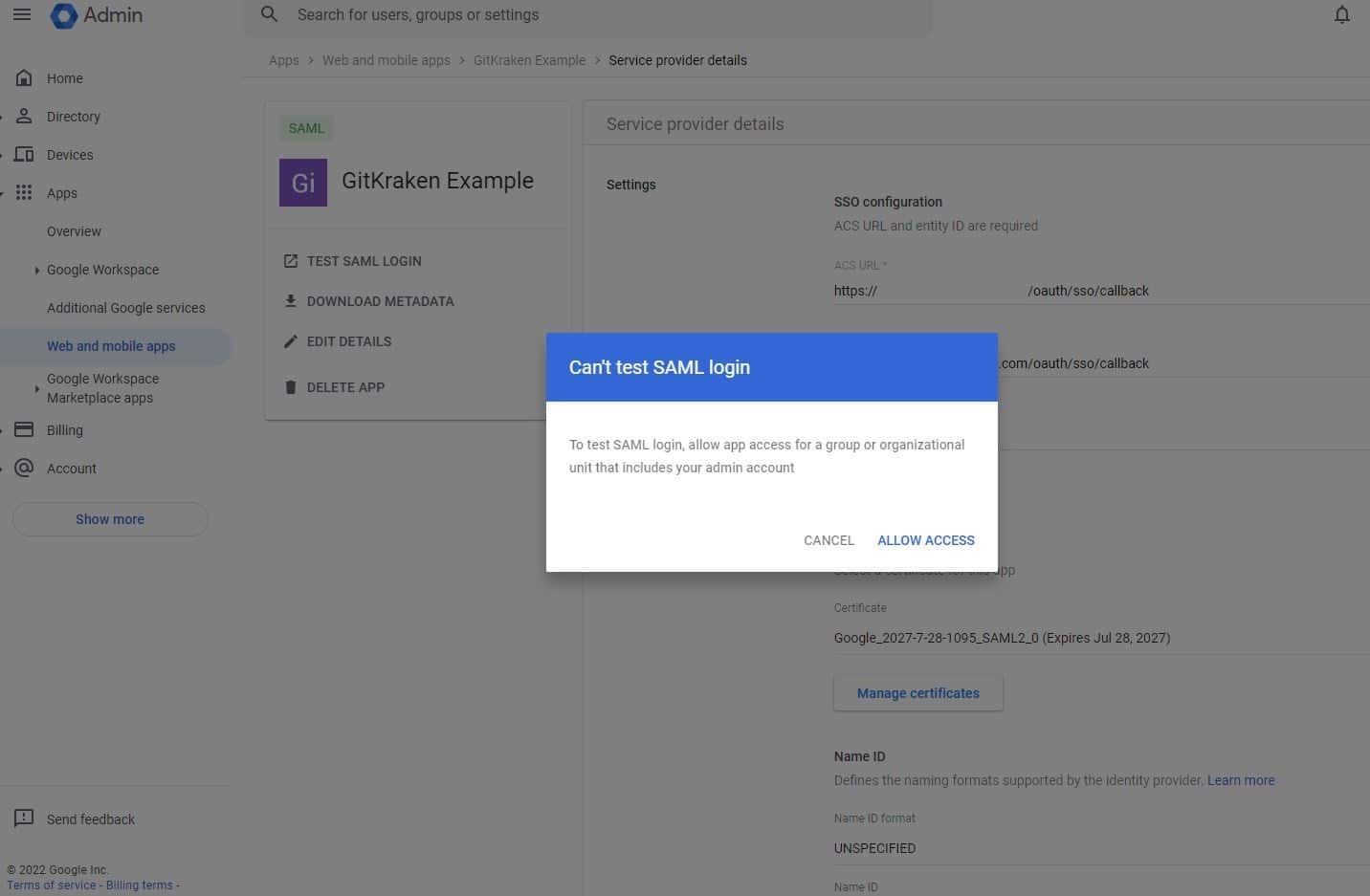
Grant access to the app - Select ON for everyone and save.
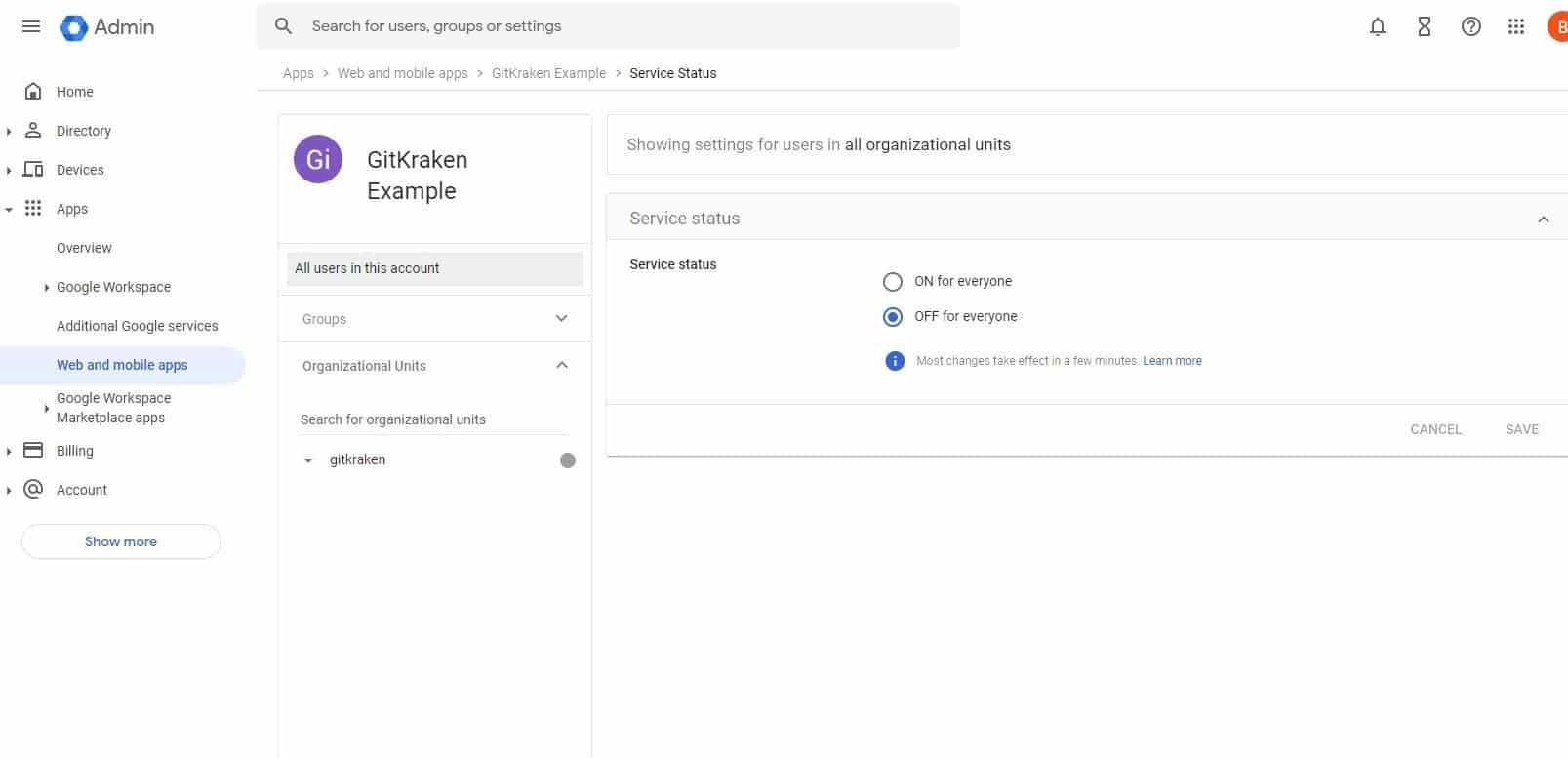
Enable the app for all users
Now you are all set to set up your SSO on a GitKraken Organization.
Azure Active Directory
How to create SAML application in Azure Active Directory:
- In a browser, go to Azure login portal.
- Enter your azure credentials and login.
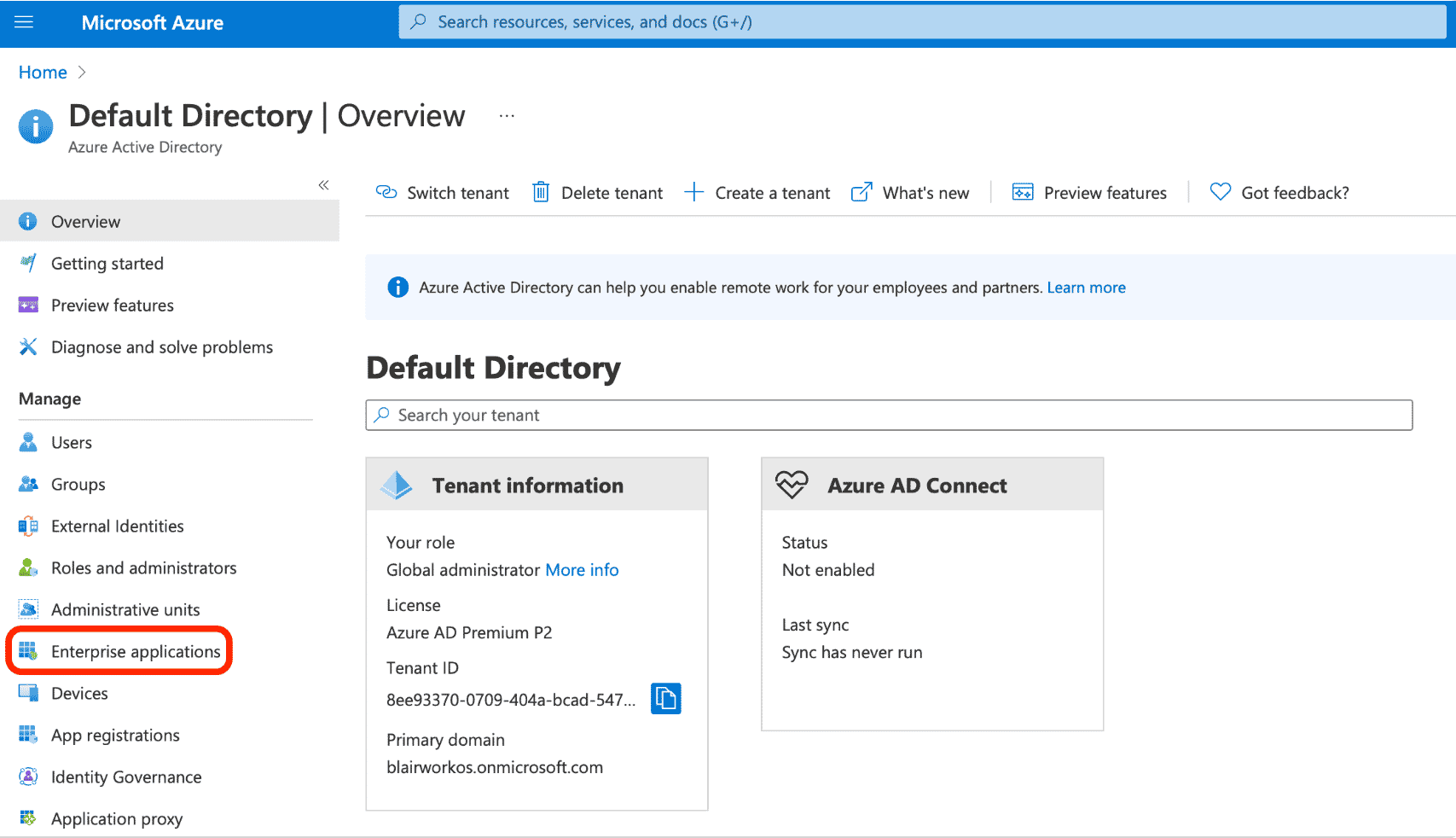
- Go to Azure Active Directory from search bar.
- In the left menu click on Enterprise applications.
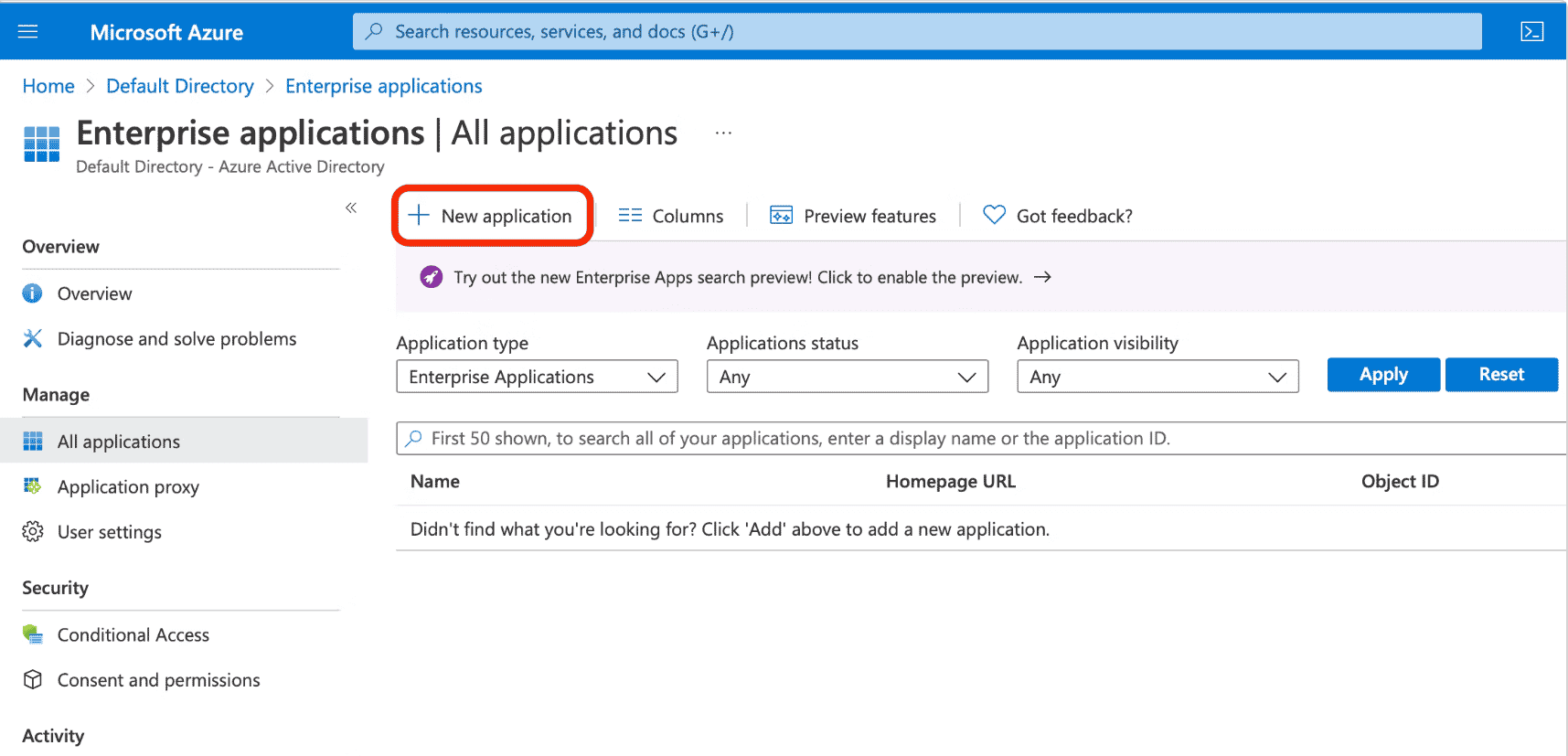
- Click on New application from the top of the page.
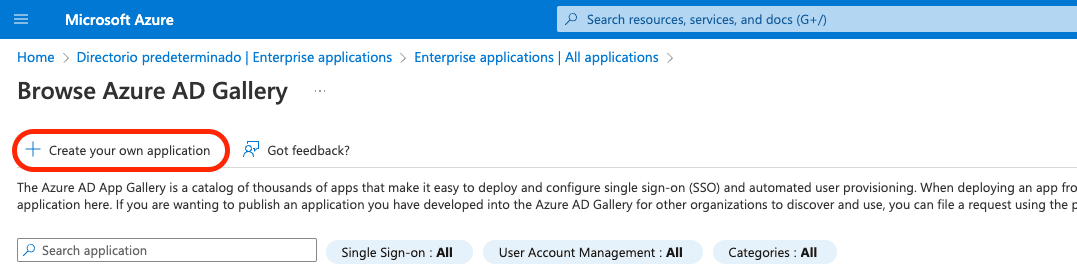
- Select Create your own application.
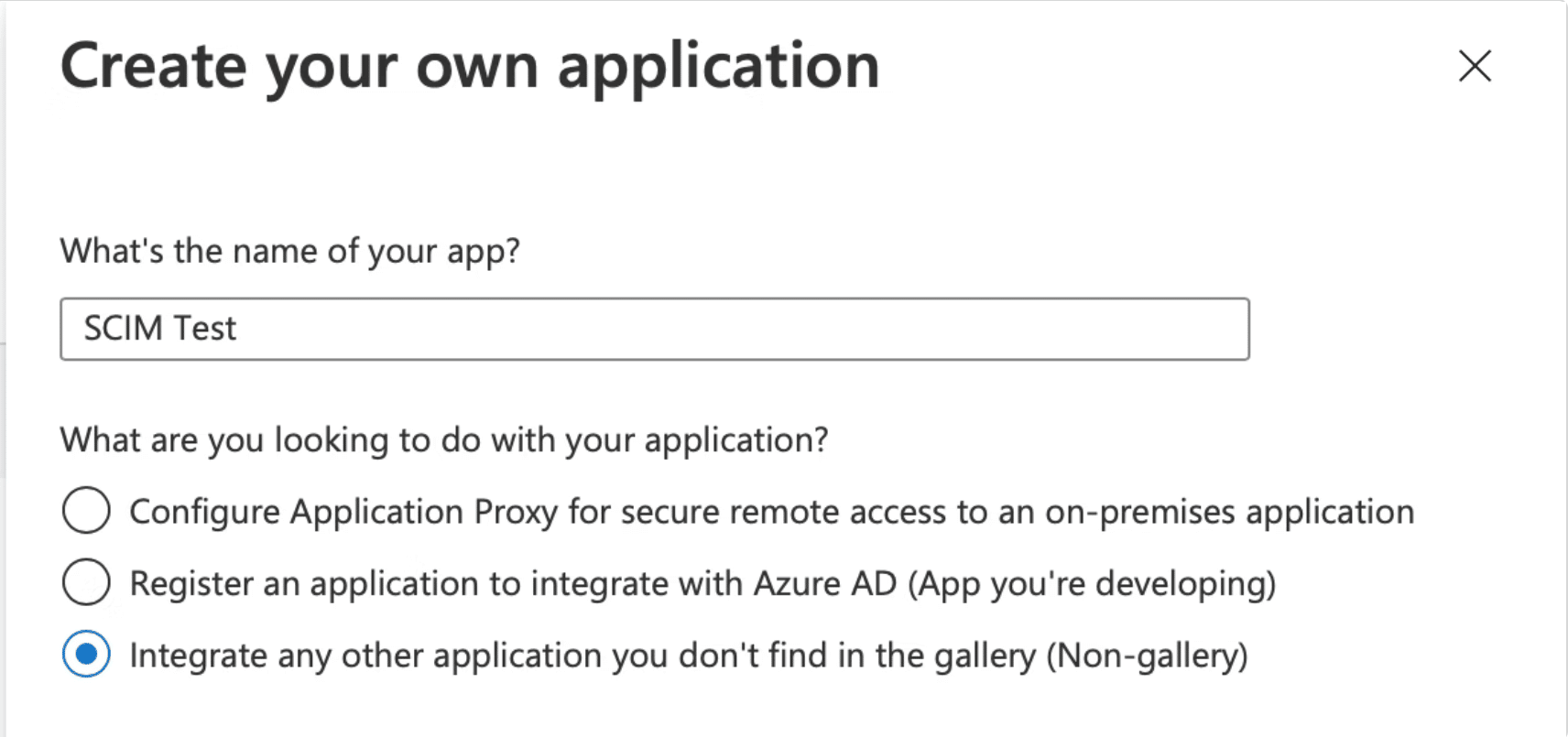
- Give your application name (such as “GitKraken SSO”) and select “Integrate any other application you don’t find in the gallery (Non-gallery)”.
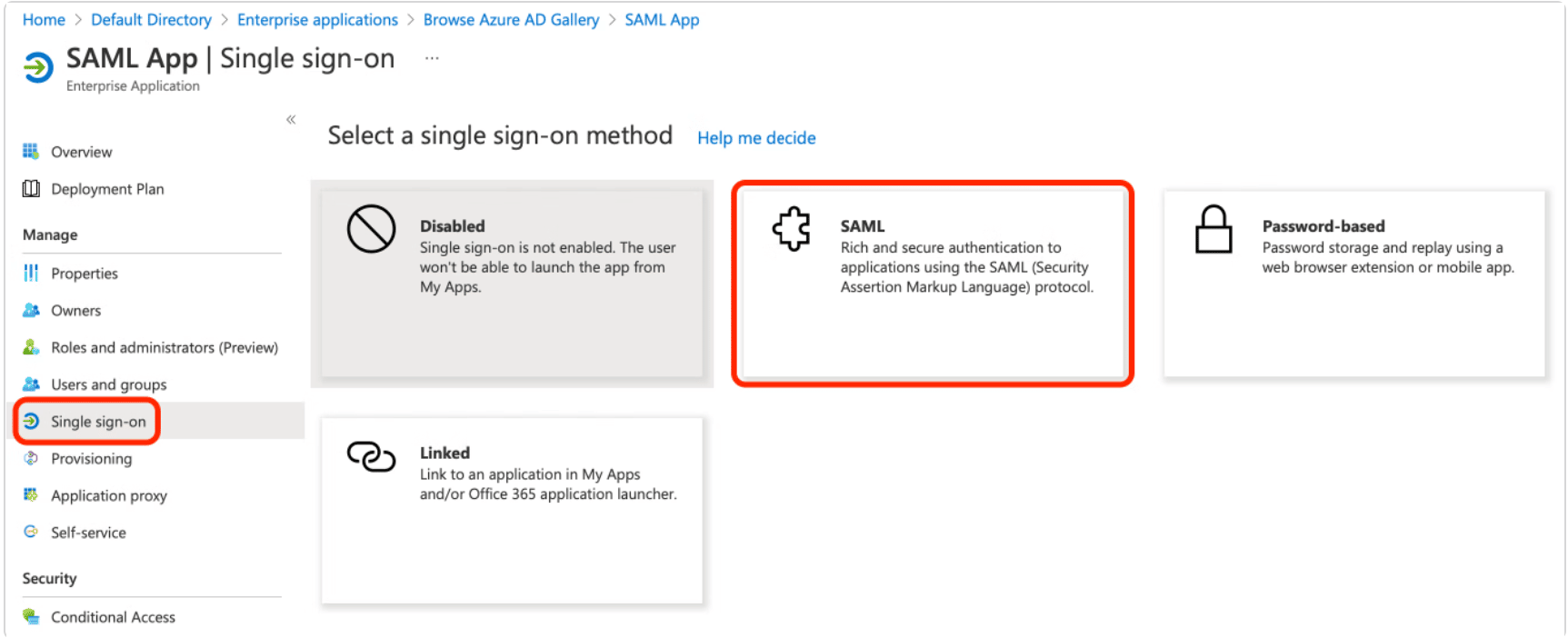
- Select Single sign-on from the left sidebar and then choose SAML.
- Click the edit icon in the top right corner to configure SAML.
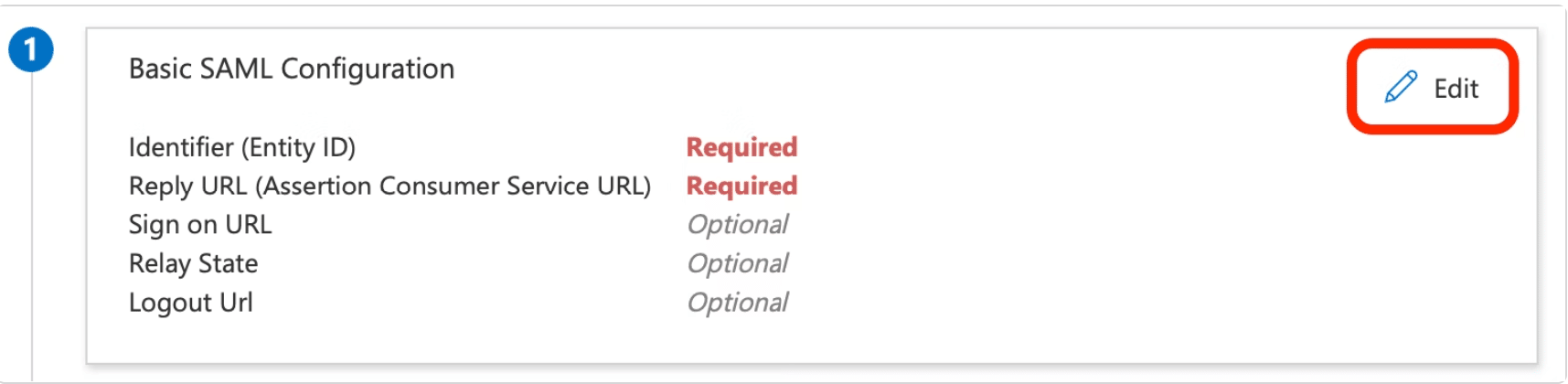
- Input the Entity ID URI and Reply URL. Both of these should direct to
https://api.gitkraken.com/oauth/sso/callbackfor GitKraken SSO.
Now you are all set to setup your SSO on a GitKraken Organization
Okta
Note: Logging through Okta Dashboard is not supported.
How to Create SAML Application in Okta:
- In a browser go to the Okta login page.
- Enter your Okta credentials and login.
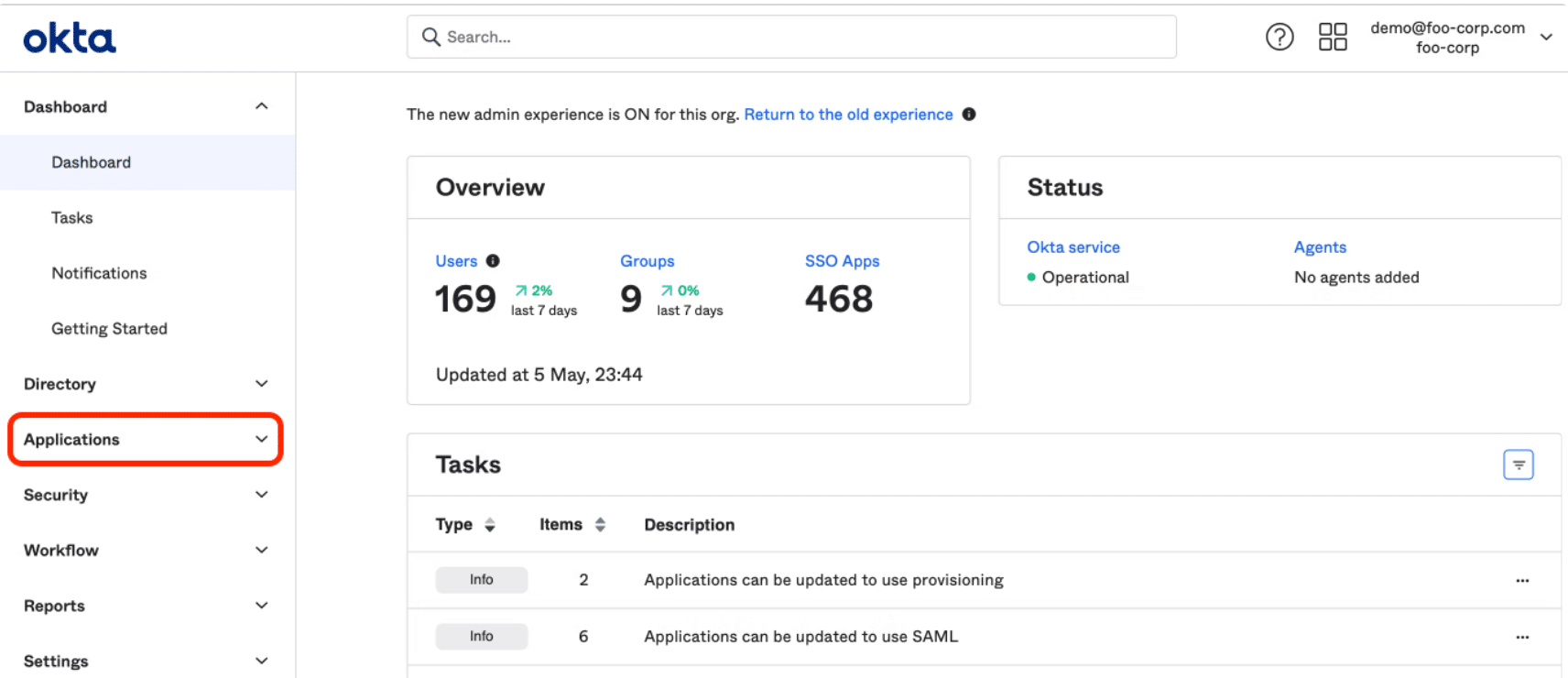
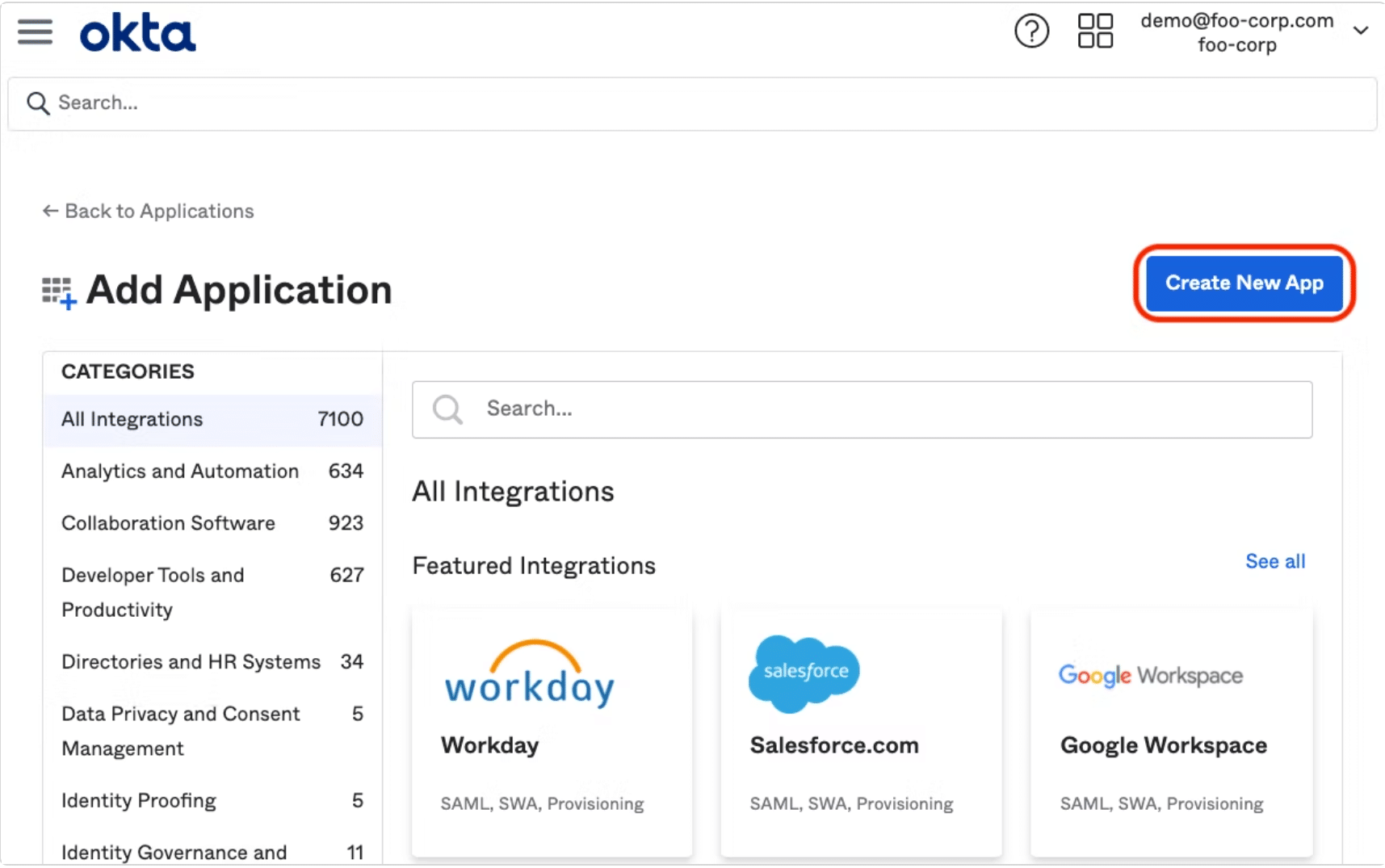
- Go to admin dashboard and select Applications in navigation bar.
- Click on Add Application.
- Select Create New App.
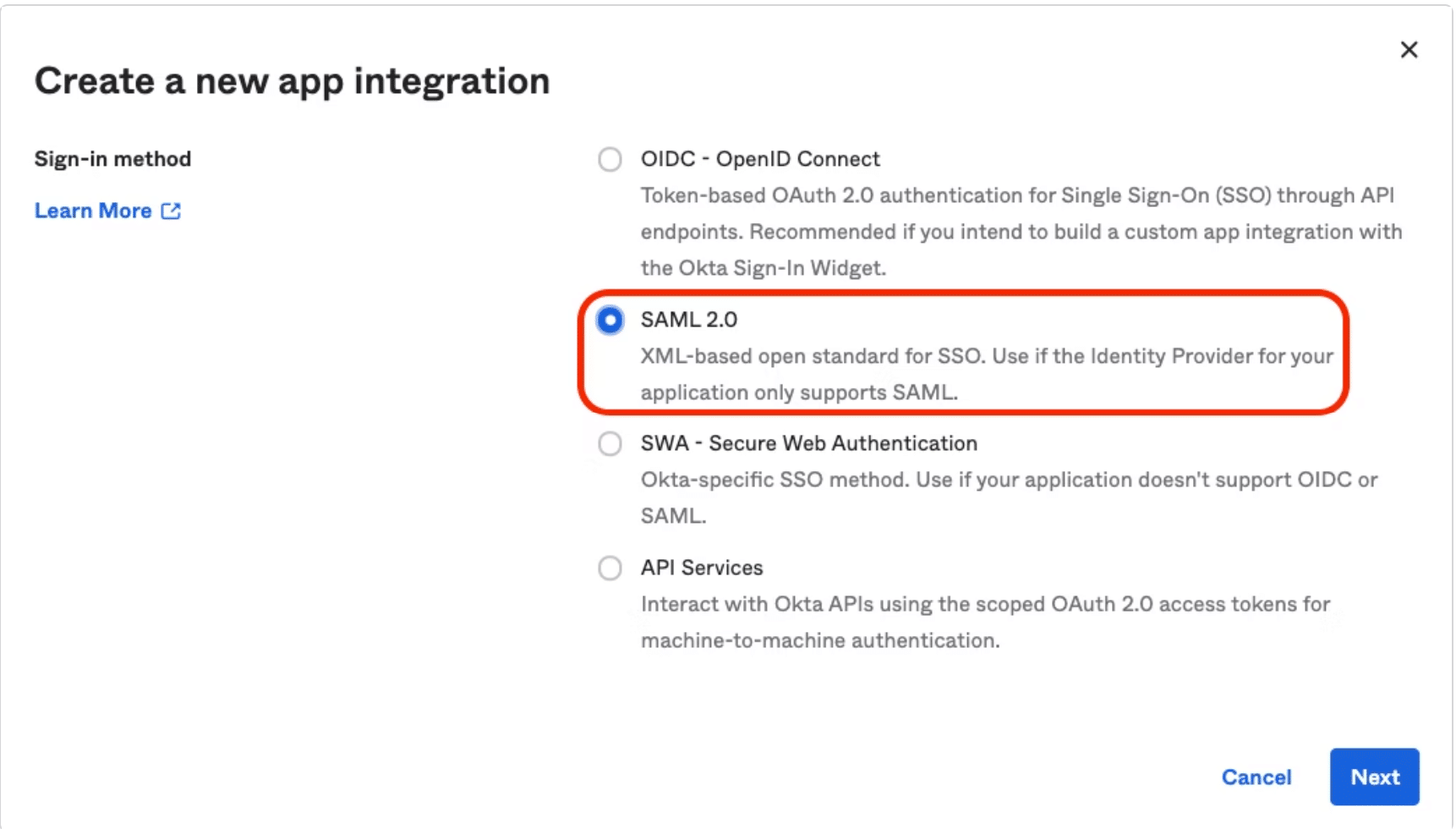
- Select SAML 2.0 as a Sign on Method and click to next button.
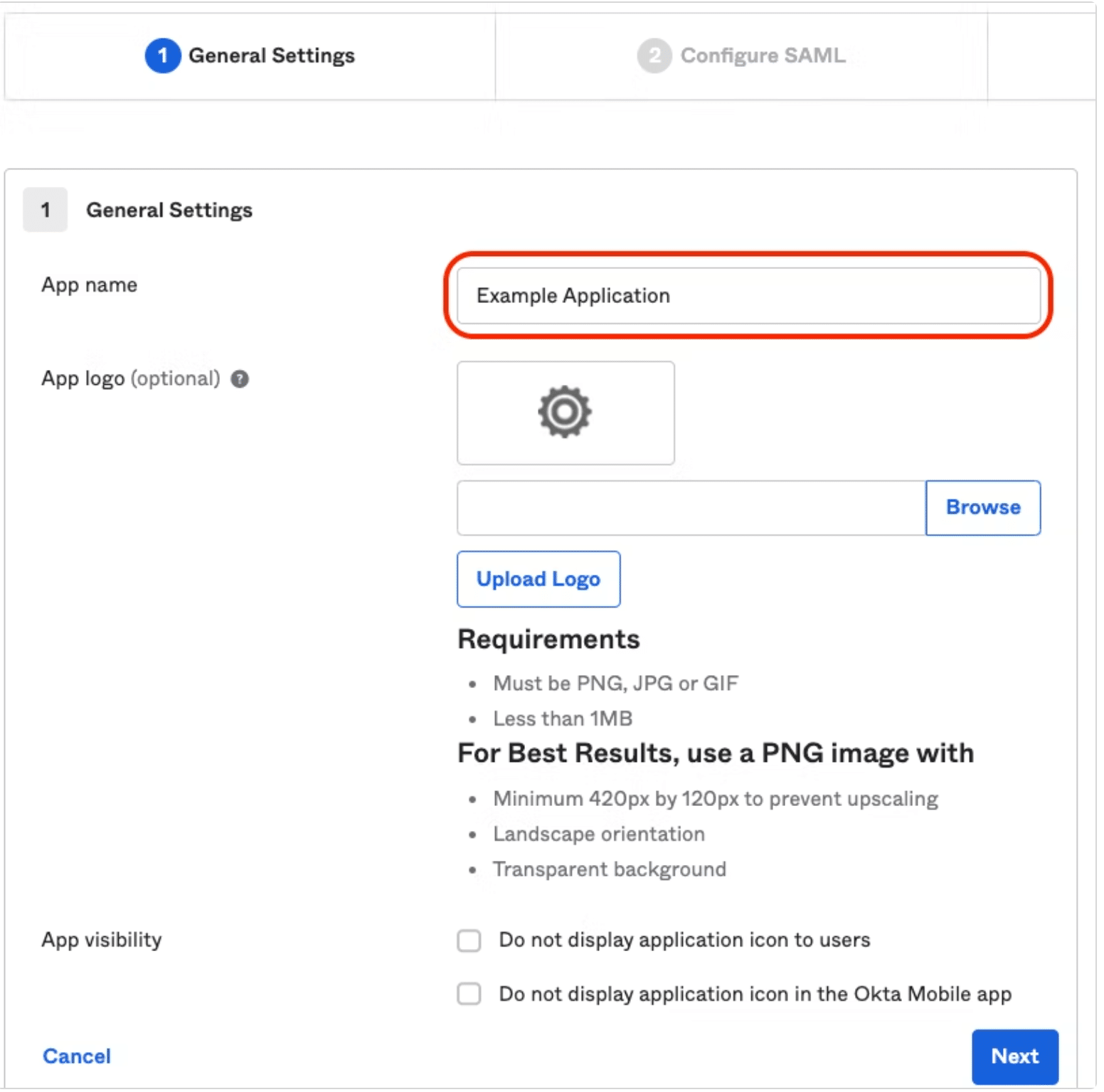
- Enter a name of application (such as “GitKraken SSO”).
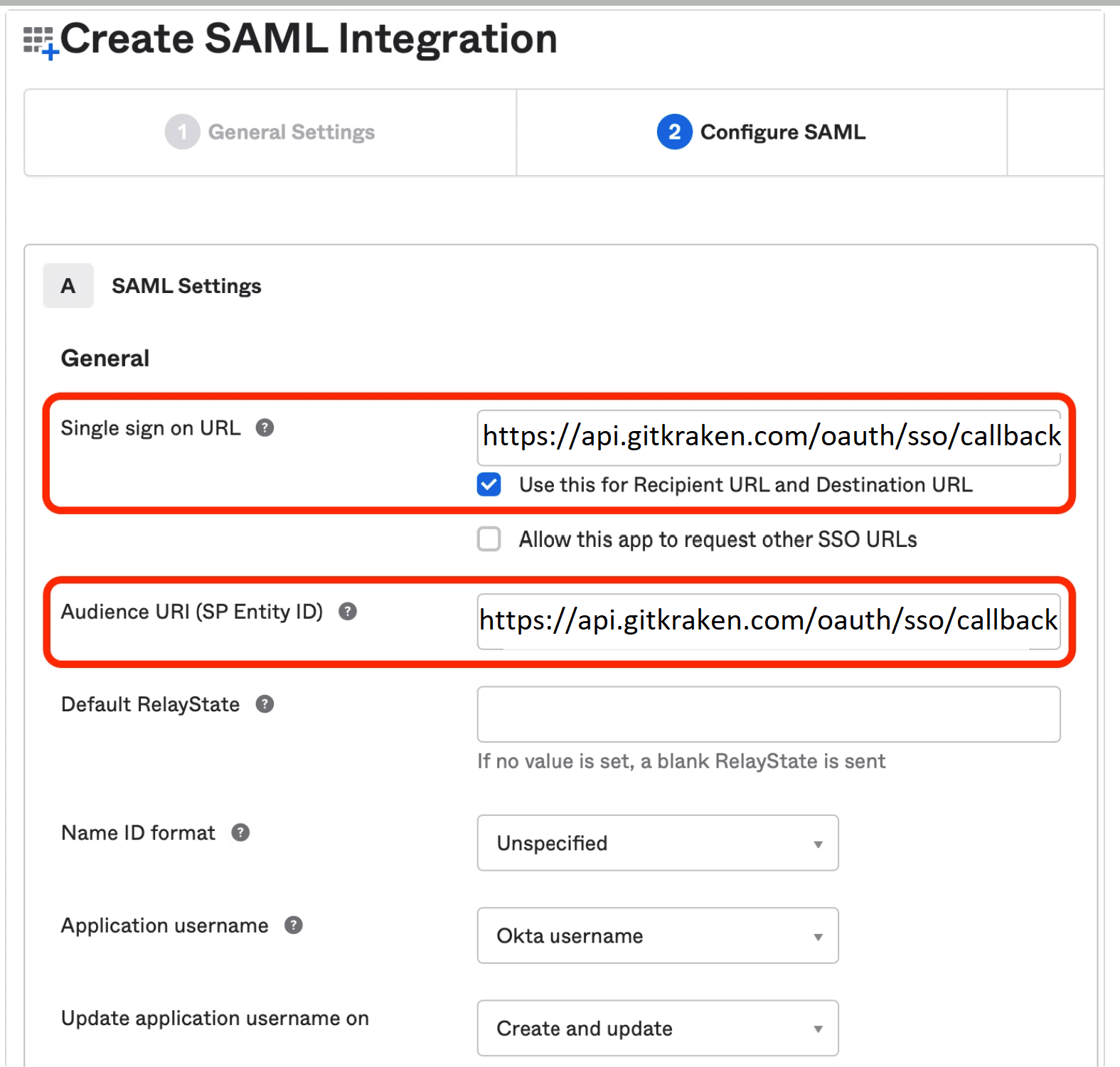
- Configure SAML Integration. The Single sign on URL and Audience URI fields should direct to
https://api.gitkraken.com/oauth/sso/callback.
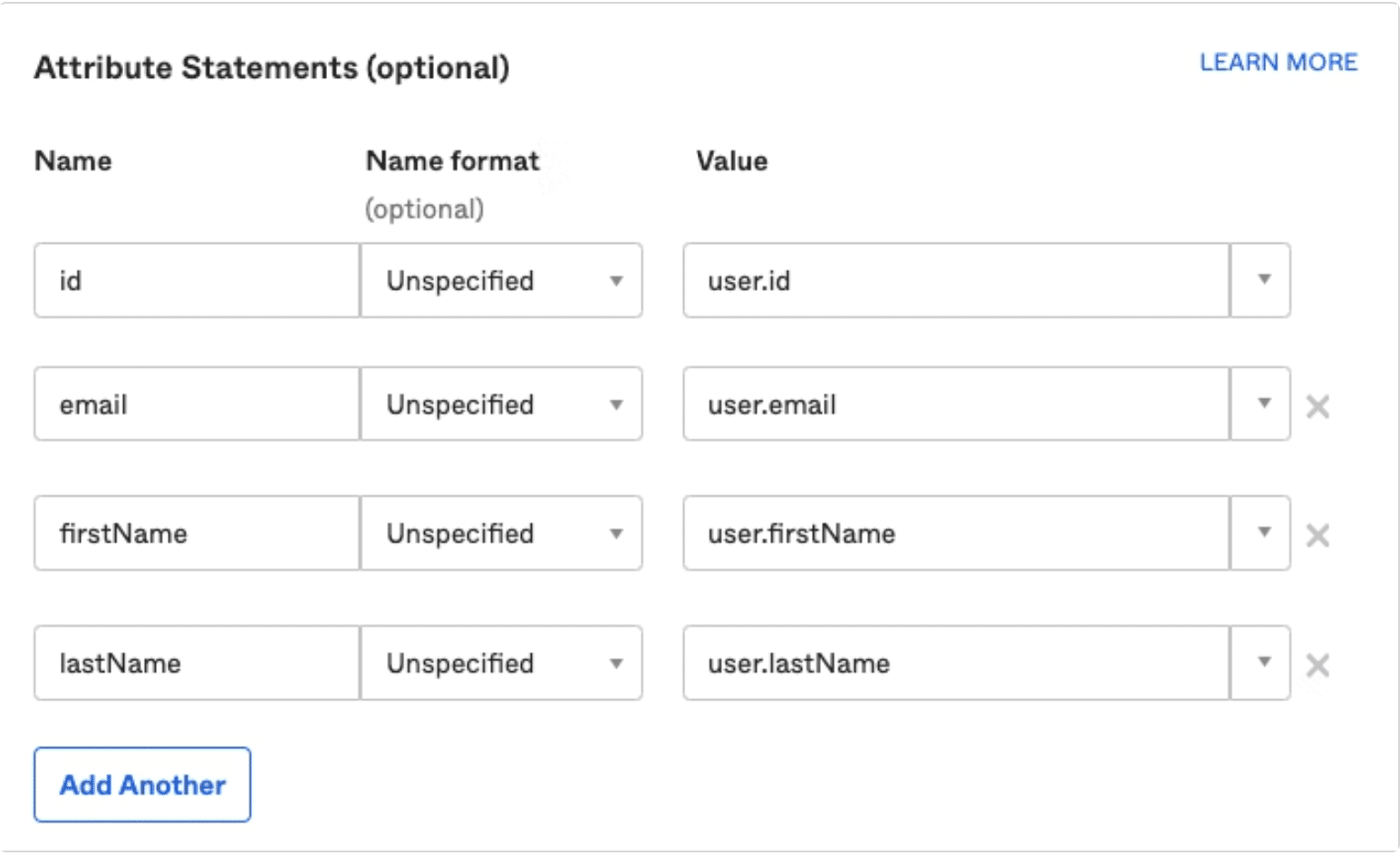
Step 9: Scroll down to the attribute statement and fill in the optional fields.
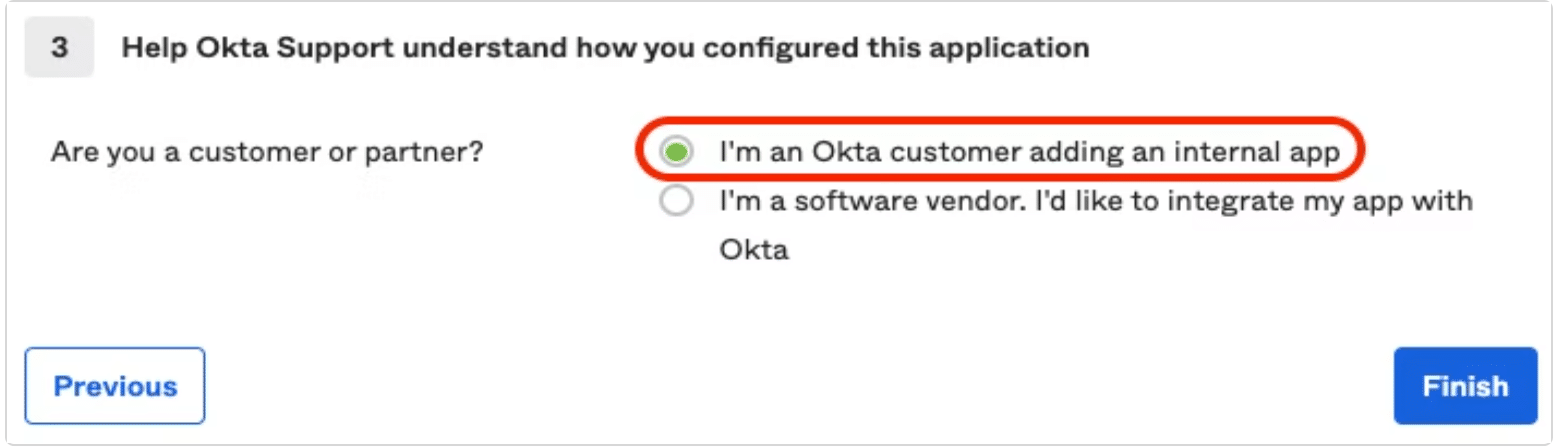
Step 10: Select “I am an Okta customer adding an internal app” from option menu and then click to finish.
Now you are all set to setup your SSO on a GitKraken Organization
Ping Identity
How to Create SAML Application in Ping Identity
-
Go to https://www.pingidentity.com/en/account/sign-on.html
-
Create an account or sign in your existing one.
-
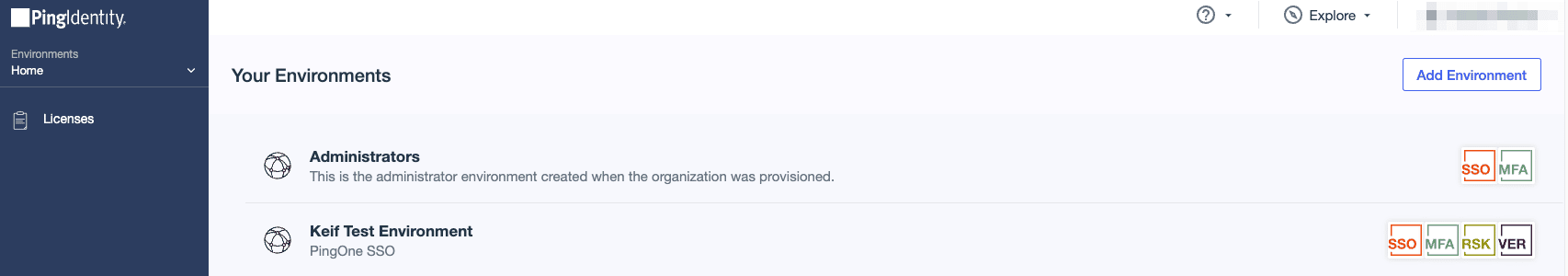
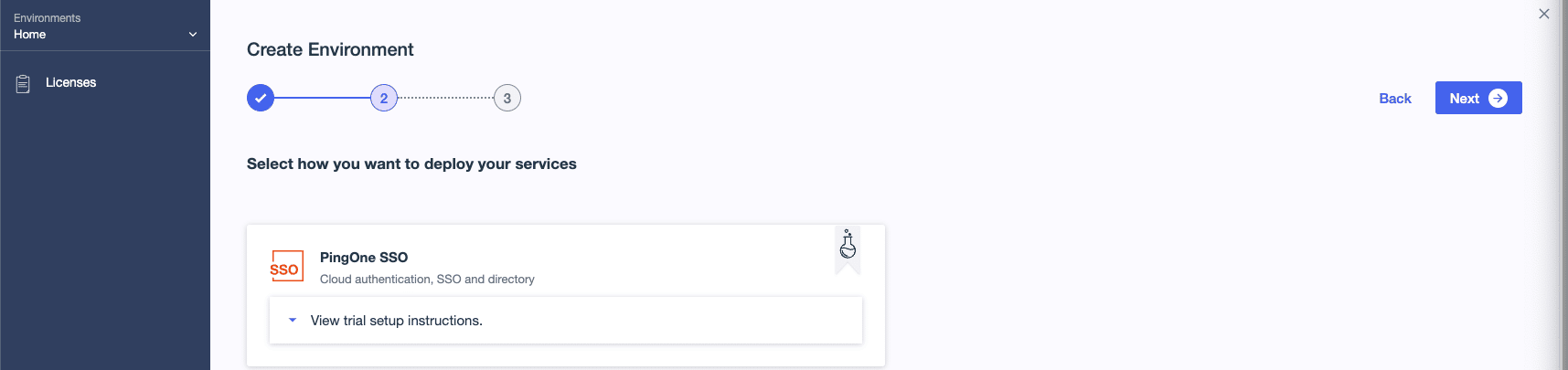
Go to the home page and click on Add Environment.
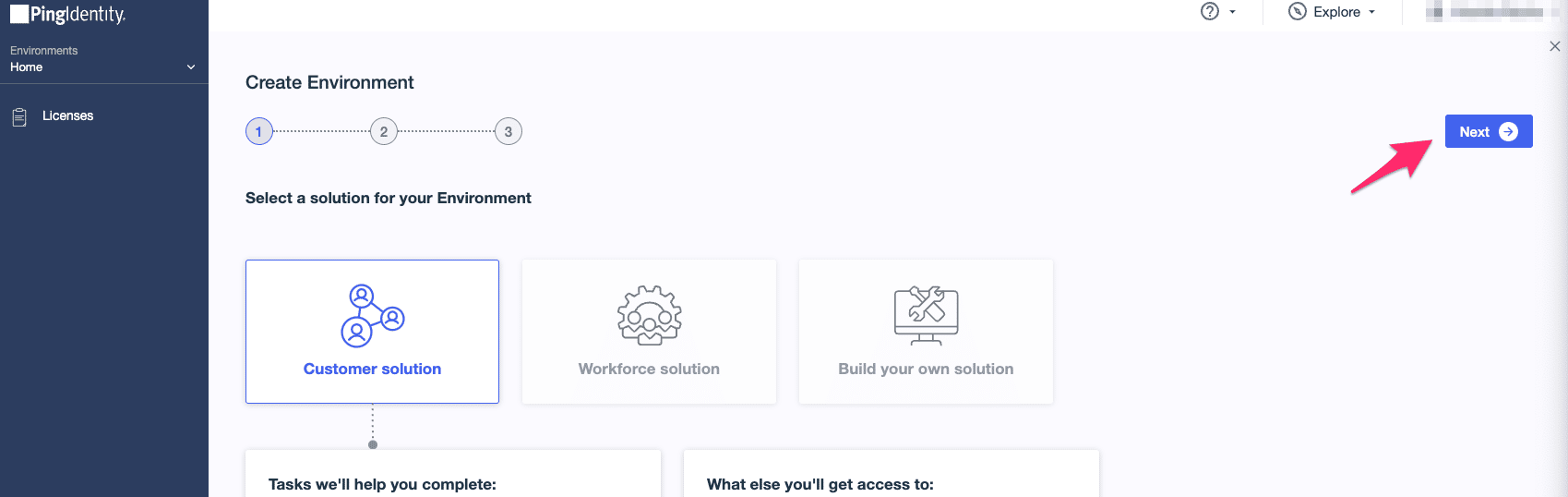
- Select the appropriate solution based on your need (in this guide, we use Customer solution) and click Next.
- Select PingOne SSO, then click Next.
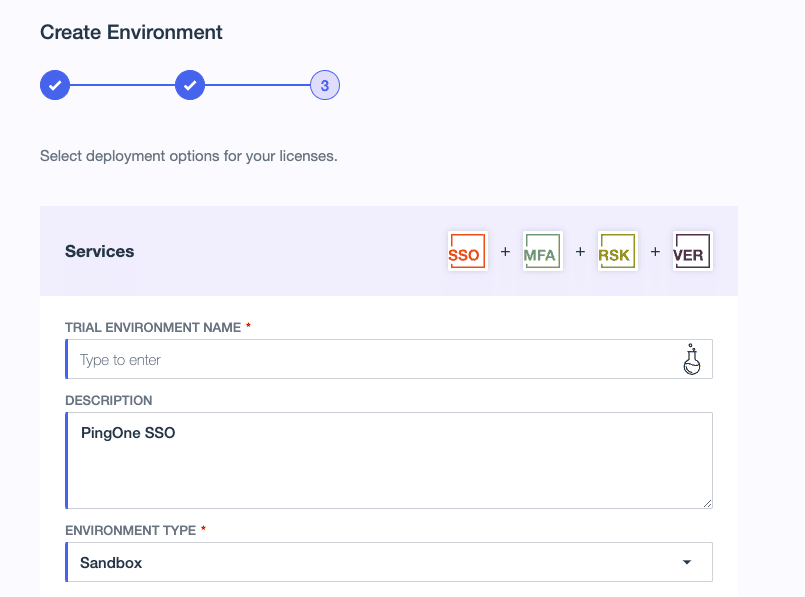
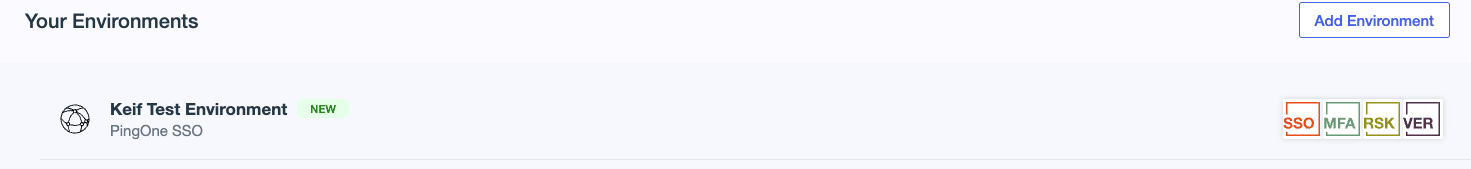
- Type in your environment name (in TRIAL ENVIRONMENT NAME), then click Finish. Now your environment is created. Go ahead and click on it.
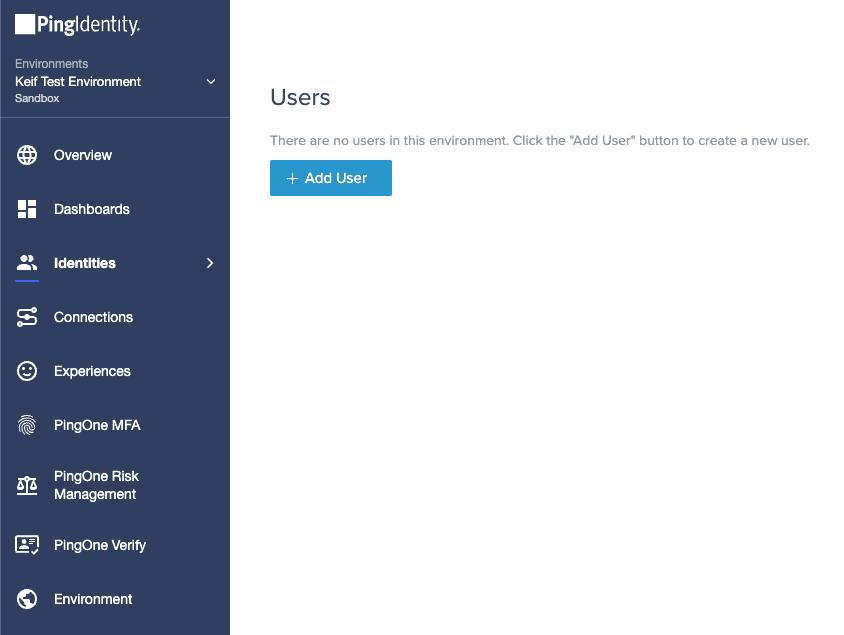
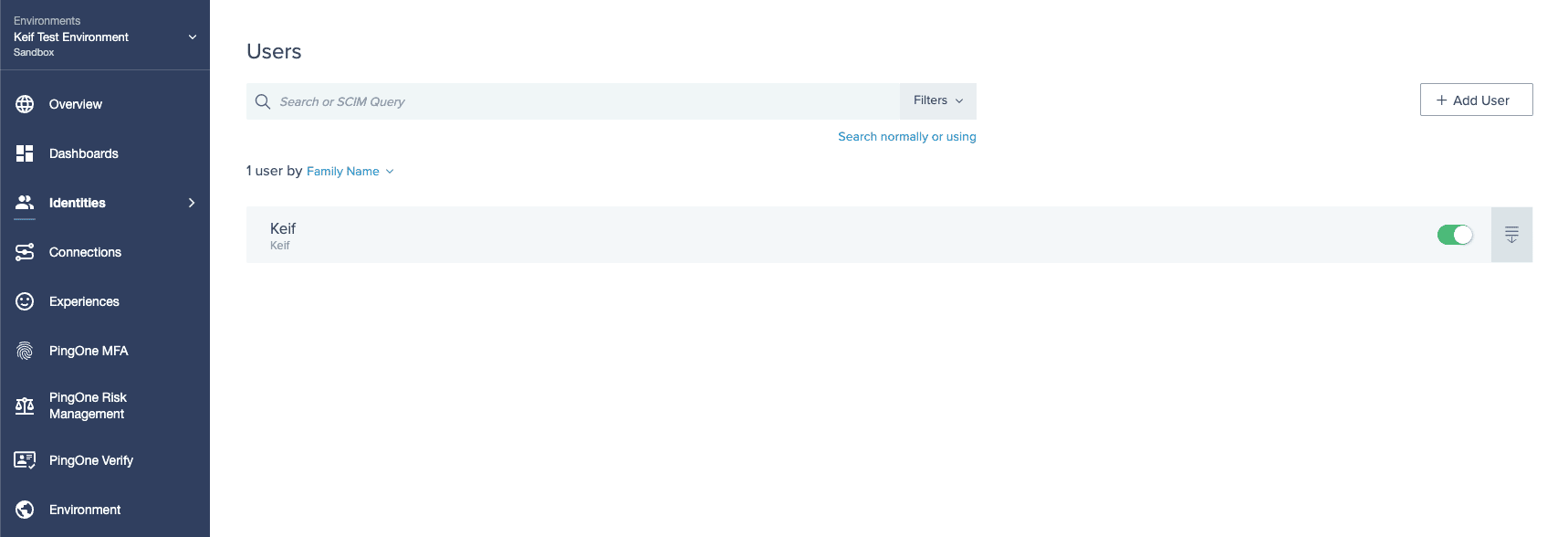
- Select Identities to add some users. Once you are done adding them click on Groups, and then click on the plus button to add a group. (Make sure to add users with their email addresses).
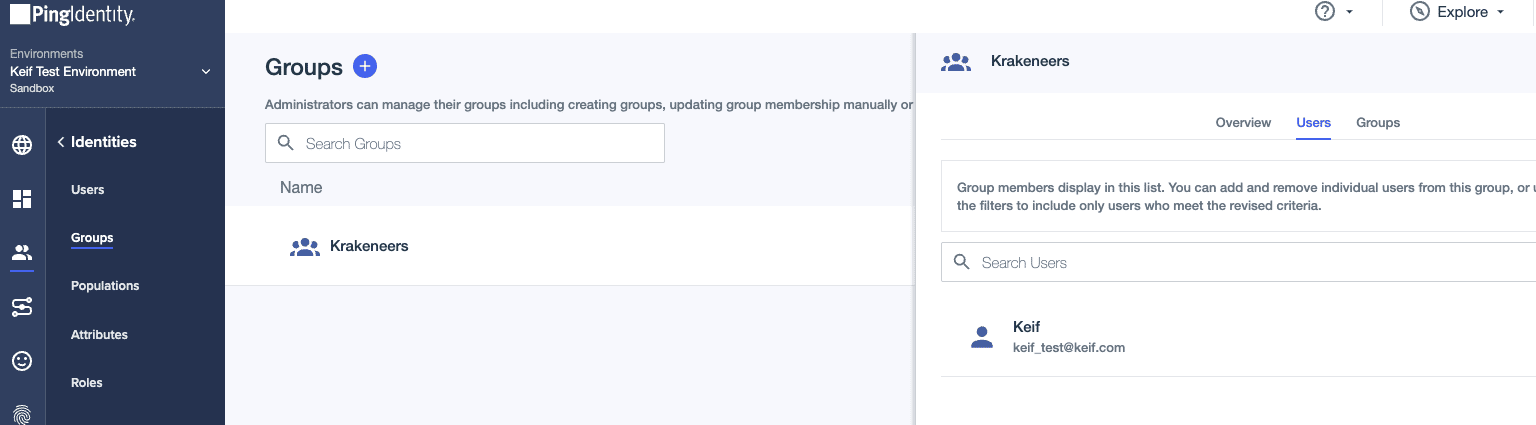
- Select Groups, then click on the plus button to add a group. Once you have that, you can add the users to your group.
- Select Connections.
- Click on the plus button.
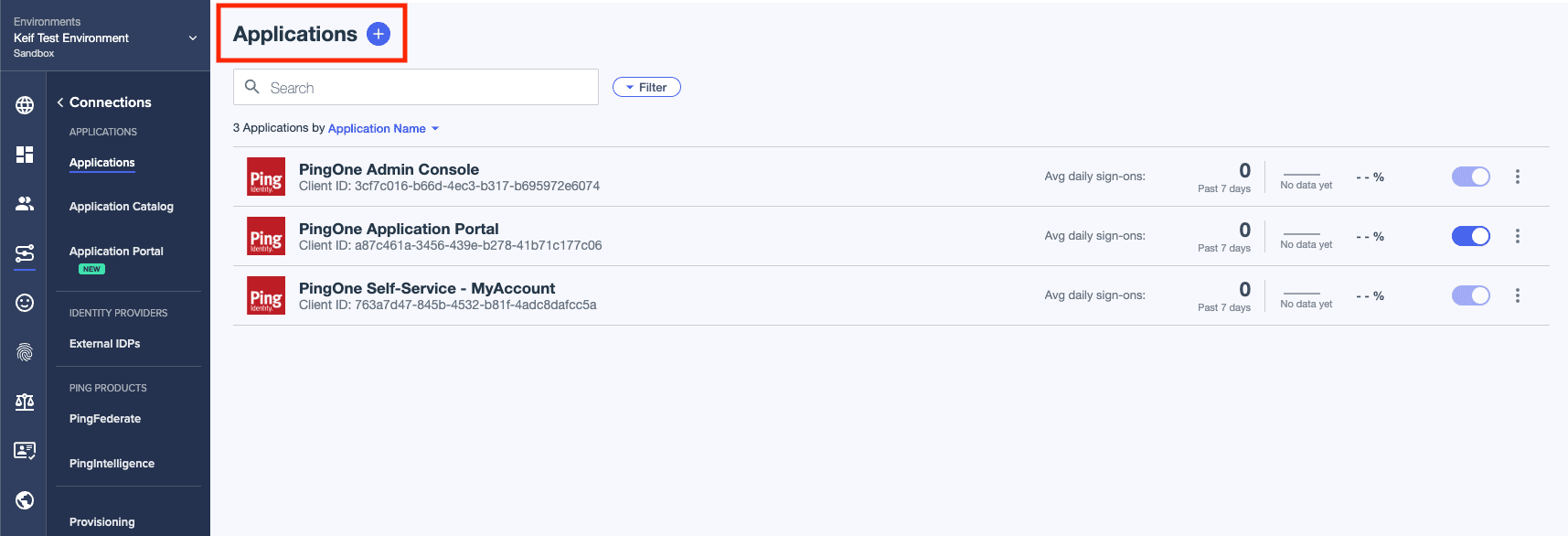
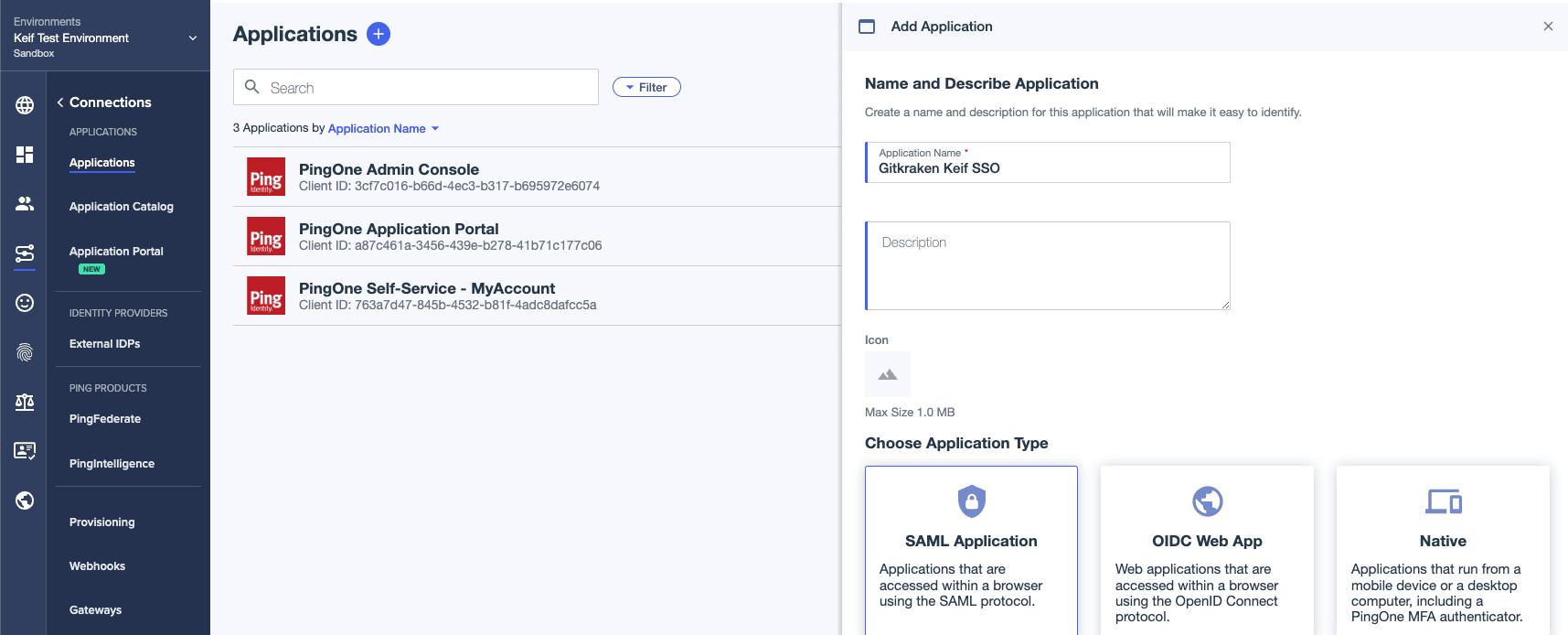
- Enter a name for your application, then select SAML Application. Next click on the Configure button which appears once you select your application type.
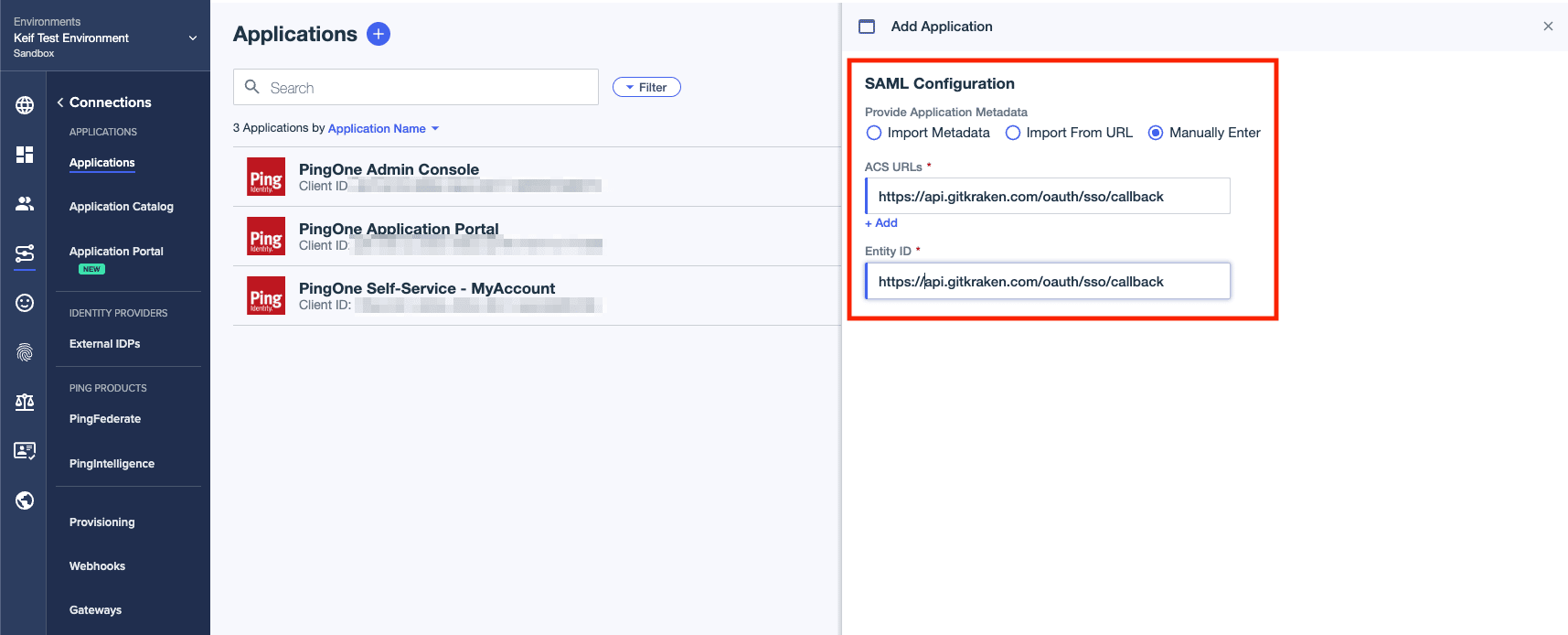
- Select Manually Enter. Type in the URL for ACS URLs and Entity ID, then click on Save.
(URL:https://api.gitkraken.com/oauth/sso/callback)
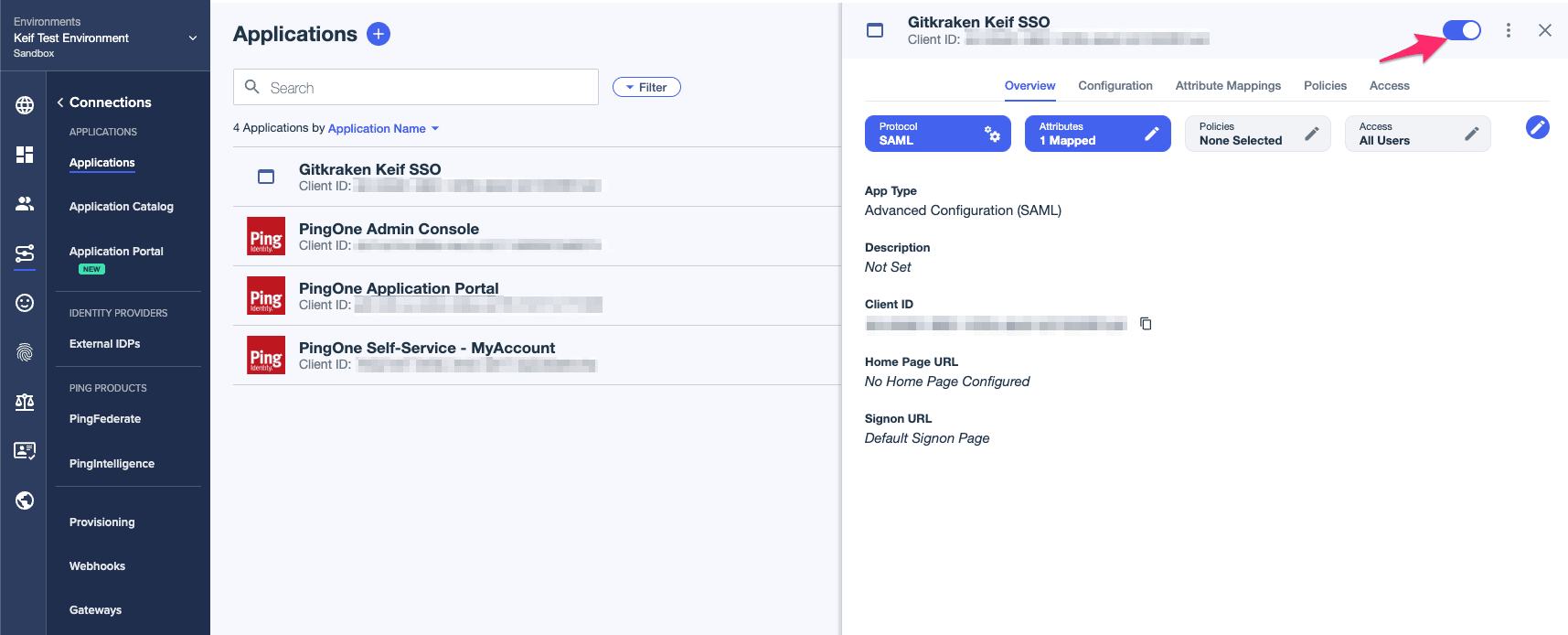
- Click on the toggle button so the users would have access to your application.
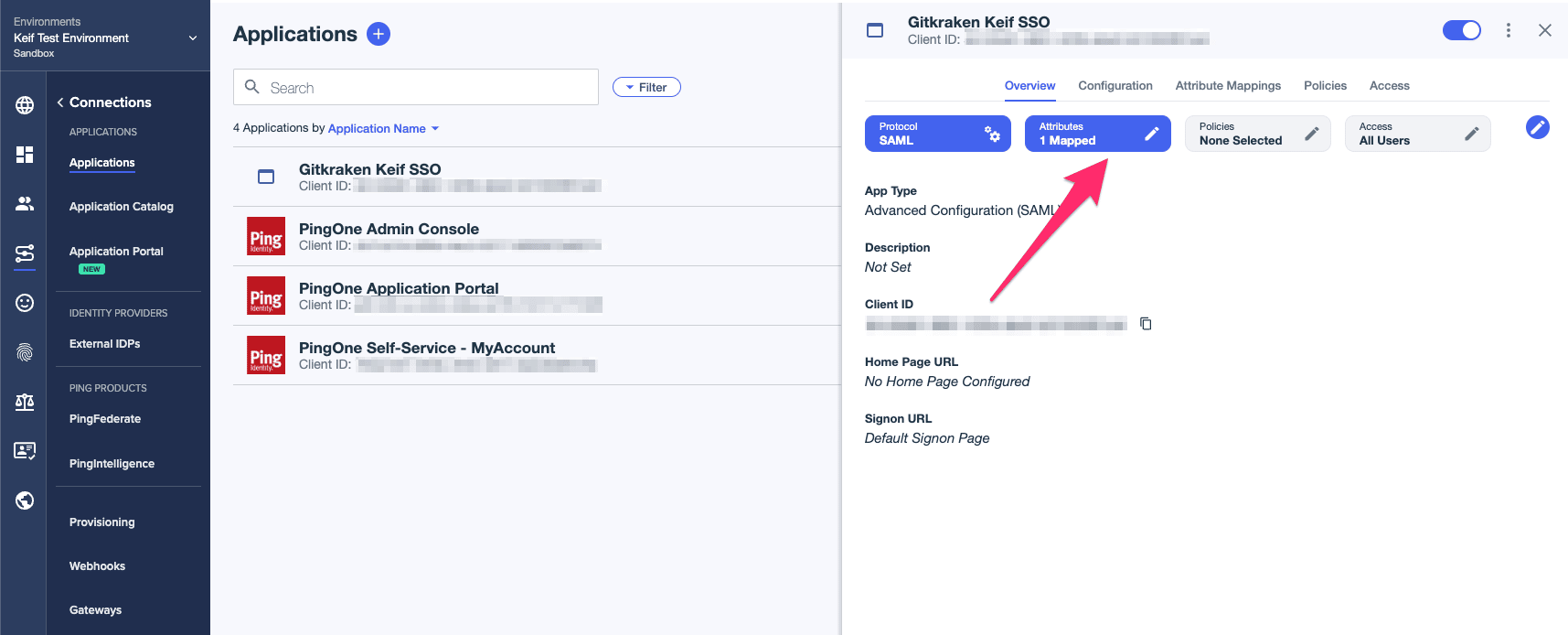
- Click on Attributes then add email as your new attribute.
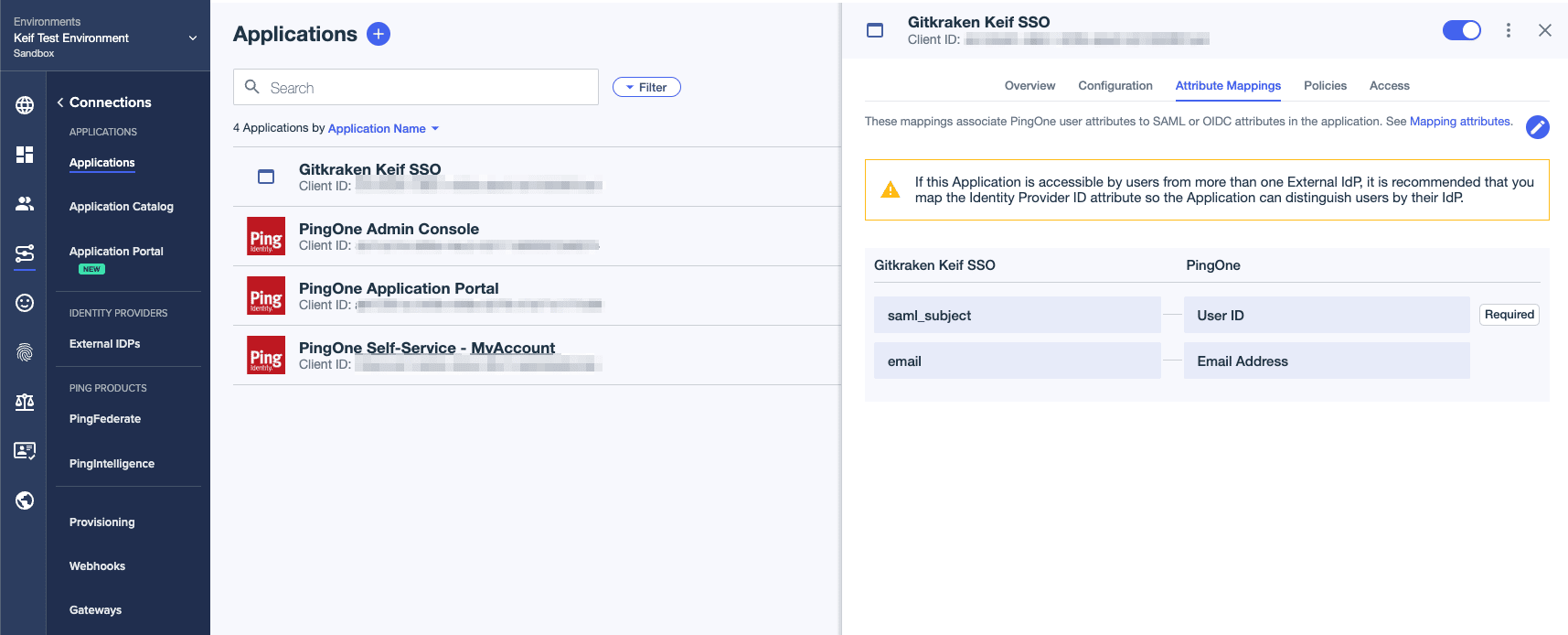
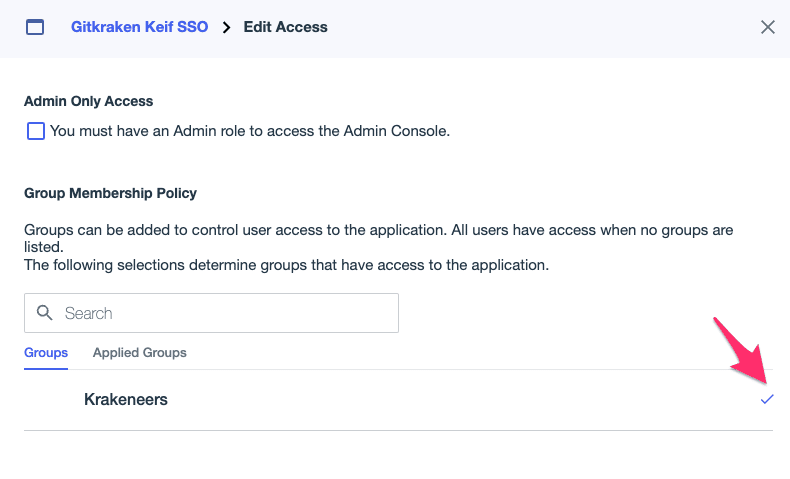
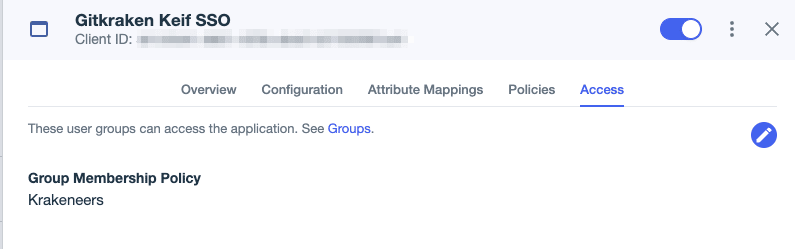
- Time to add the group we created in Step 8.
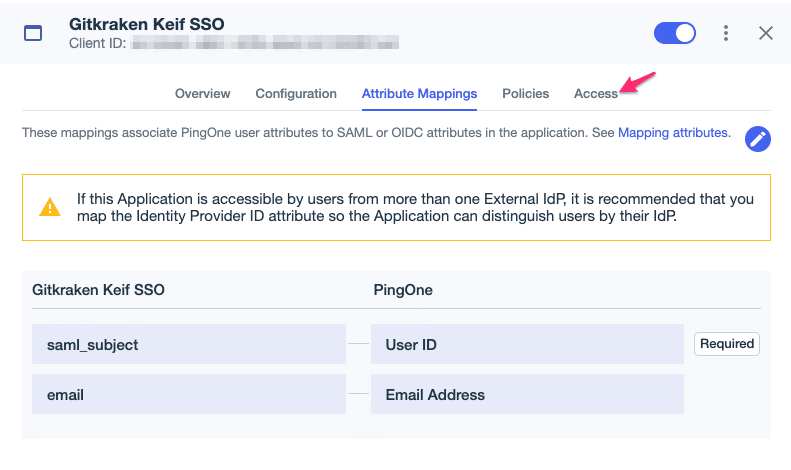
- Select the pencil icon pictured below.
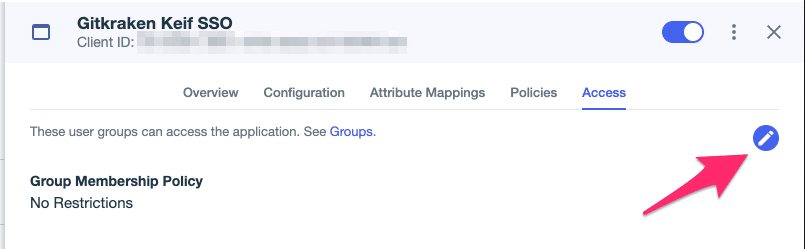
- Click on the plus icon to add the group, then click on Save.
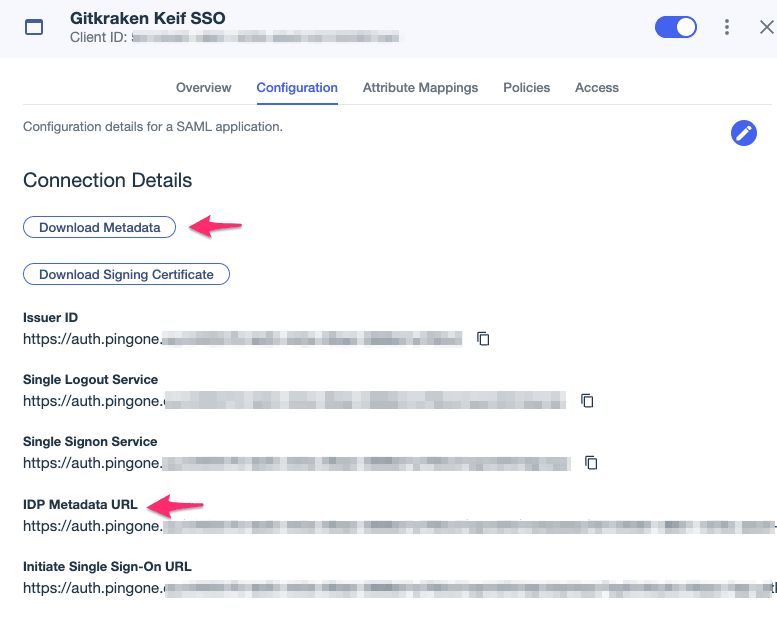
- Go to the Configuration tab to copy your IDP Metadata URL and download your metadata (Download Metadata button).
-
Log into gitkraken.dev/settings/sso and select “Setup SSO”. Type in your Connection name and Domain.
-
Then use the IDP Metadata URL and Metadata from step 18 for Metadata URL and Metadata. Click on Create Connection

- Now the users who were added in step 7 can Sign in with SSO.